The production and maintenance of particular documents and controls that describe an organization’s information security policies, procedures, and processes is one of the essential conditions for ISO 27001 documentation. These required records provide the framework for achieving and proving conformity to ISO 27001 requirements.
There are a huge number of lists of main papers needed to comply with ISO 27001 standards. Each of these papers is essential to various phases of implementing ISO 27001, ensuring a methodical and organized approach to information security management. However, not every single piece of additional documentation is required, but just to be safe, secure, and certified is preferable to being sorry, as we always say.
In this article, we will get to know the documents and controls needed to help comply with ISO 27001. To make it possible for organizations to comply with ISO 27001, it is important that they understand the mandatory documents that are needed. Organizations may build a solid basis for information security management by properly applying these documents and controls and protecting the confidentiality, integrity, and accessibility of their important data assets.
MANDATORY RECORDS OF ISO 27001
WHAT IS THE IMPACT OF THE ISO 27001:2022 REVISION ON MANDATORY DOCUMENTS AND RECORDS?
WHAT ARE THE MANDATORY DOCUMENTS OF ISO 27001?
HOW MANY MANDATORY CLAUSES ARE THERE IN ISO 27001?
WHAT ARE THE CONSEQUENCES OF MISSING ISO 27001 MANDATORY DOCUMENTS?
GET A PROFESSIONAL HELP FROM CERTPRO
MANDATORY ISO 27001 DOCUMENTS
“ISO 27001 Documentation” is an important part of the ISO 27001 Certification process, including a variety of actions designed to demonstrate conformity with the standard’s criteria. This documentation includes details on how an organization incorporates the Information Security Management System (ISMS) into its operational structure, processes for mitigating security risks and cyberattacks, and the execution of security policies alongside risk assessments.
The creation of an information security policy is crucial to ISO 27001 documentation, as it acts as a fundamental document outlining the organization’s commitment to protecting its data assets. This policy defines the organization’s roles and responsibilities for data quality and security procedures. Organizations that follow the ISO 27001 mandatory documents process not only demonstrate conformity with international standards but also create a strong framework for effectively managing information security risks and protecting sensitive data.
Scope of ISMS: This clearly identifies the business sectors that your ISMS covers for your stakeholders. You could wish to include a vision statement and/or plan along with the ISMS scope to provide your stakeholders with more clarity. Remember that the main component of a successful certification is your specified ISMS scope.
Information security policy: Top management must create an information security strategy that is pertinent to the goals of your particular organization. The policy demonstrates senior management’s dedication to the ISMS goals and the ongoing development of those goals.
Risk assessment and treatment: You must demonstrate how you recognize, examine, rank, and prioritize your information threats. Make the decisions that are right for your organization, and then put them in a report, a list, a matrix, or any other compelling document that demonstrates how your risks are being managed.
Statement of Applicability (SoA): The control goals and controls chosen for implementation inside the ISMS are identified and justified in the Statement of Applicability (SoA), which is a document. It lists the security measures from ISO 27001 Annex A that have been selected and justifies their applicability in the organization’s particular situation. The SOA assists in making sure that the chosen controls complement the organization’s risk profile and adequately safeguard its information assets.
Risk treatment plan: The activities and steps that must be taken to address the risks that have been identified are described in the risk treatment plan. It offers a step-by-step guide for carrying out risk management procedures, such as the adoption of certain security controls or other risk mitigation techniques. The strategy includes information on who is in charge of carrying out each step, timetables, and monitoring systems to guarantee successful risk management.
Information Security Objectives: Information security objectives are definite targets that a company establishes for its ISMS. These goals represent the organization’s priorities and ideal information security results and are in line with its information security policy. Increasing the protection of sensitive data, expanding incident response capabilities, or raising staff knowledge and training are a few examples of information security goals.
Risk assessment and treatment report: The risk assessment process, results, and risk treatment choices made by the company are all thoroughly covered in the risk assessment and treatment report. It details the outcomes of risk analyses, including identified hazards, their likelihood, and consequences, as well as the organization’s risk management choices. The report aids in proving compliance with ISO 27001 criteria and acts as a reference for continuing risk management initiatives.
Inventory of assets: All information assets inside an organization are identified and listed in an inventory of assets. As well as intangible assets like intellectual property, confidential information, and sensitive data, this also encompasses tangible assets like hardware, software, and data repositories. Organizations may better understand their asset landscape by doing an inventory, evaluating their worth and importance, and putting in place the necessary security safeguards to secure them.
Acceptable use of assets: The policies and procedures that outline how employees, independent contractors, and other authorized users should utilize organizational assets are referred to as acceptable use of assets. To guarantee correct usage, guard against misuse, and reduce security risks, these rules specify acceptable behaviors, access limitations, and responsibilities connected to the use of assets.
Incident response procedure: An incident response procedure specifies the procedures and actions to take in the event of a security incident or breach. It offers a methodical method for recognizing, reacting to, containing, looking into, and recovering from security problems. To reduce the effects of crises and quickly resume regular operations, the method specifies roles and duties, communication protocols, and escalation mechanisms.
Statutory, regulatory, and contractual requirements: These terms are used to describe the legal and regulatory standards that a company must follow with regard to information security. These requirements might consist of contractual obligations, data protection mandates, industry-specific rules, and privacy legislation. Organizations are required to recognize, comprehend, and adhere to these standards, incorporating them into their information security procedures and making sure the proper controls are in place.
Security operating procedures for IT management: IT management and security operating procedures provide standards and best practices for managing and running safe IT systems. System administration, access control, change management, vulnerability management, patch management, and incident response are all covered by these processes. In addition to ensuring the continued security and dependability of IT operations, they offer guidance and policies to reduce security risks related to IT infrastructure.
Definition of security roles and responsibilities: Clarifying the roles, duties, and accountability of individuals or teams involved in information security inside an organization is a key component of the definition of security roles and responsibilities. End users, system administrators, data custodians, and information security managers are examples of roles that fall under this category. These roles should be clearly defined to ensure that everyone is aware of their security duties, to facilitate efficient coordination, and to prevent gaps or overlaps in security-related tasks.
Definition of security configurations: The term “security configurations” refers to the process of identifying and recording the precise configurations and settings that must be applied to IT systems, apps, and gadgets in order to guarantee secure functioning. Configuring firewalls, access restrictions, encryption standards, password guidelines, and other security-related settings falls under this category. Consistently defining and executing security settings increases the overall security posture of the company’s IT infrastructure by reducing vulnerabilities.
Secure system engineering principles: The concepts of secure system engineering are a collection of standards and procedures for creating safe IT systems and applications from the bottom up. Incorporating security controls, threat modeling, secure coding techniques, and thorough testing into the system development life cycle are the main goals of these concepts. Organizations may create more dependable and secure systems that are better able to fend off emerging threats by following secure system engineering principles.
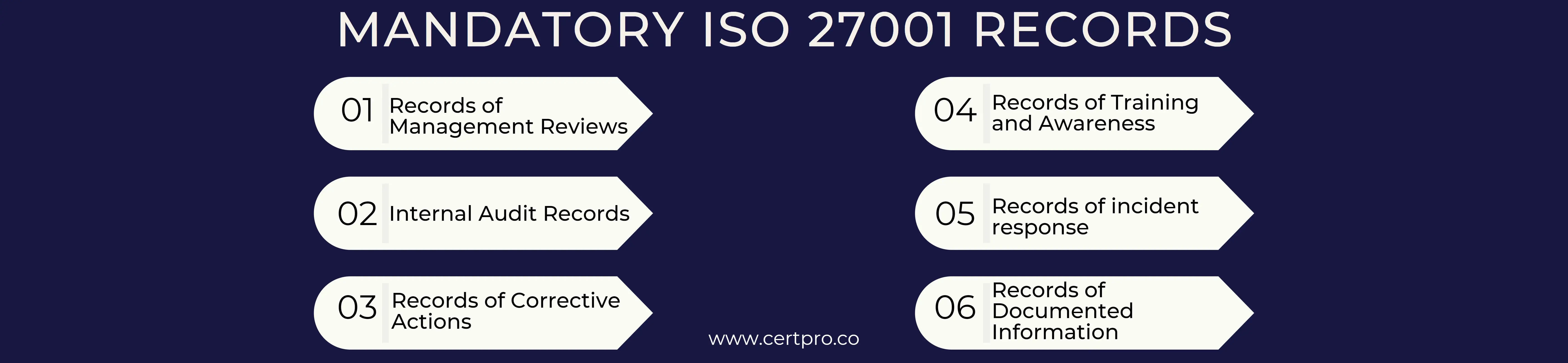
MANDATORY RECORDS OF ISO 27001
The mandatory records of ISO 27001 are:
Records of Corrective Actions: Identification of nonconformities, implementation of corrective measures to resolve them, and proof of their success.
Records of Training and Awareness: Records of training efforts, training programs, and employee involvement in information security awareness training and activities.
Internal Audit Records: Records of internal audit operations, including the audit plan, audit scope, audit results, and any remedial measures adopted as a result of the audits.
Records of Documented Information: These include policies, processes, work instructions, records, and documentation of the development, review, and management of documents pertinent to the ISMS.
Records of Management Reviews: A record of the agenda, minutes, and any decisions or actions made during management review meetings held by top management to assess the effectiveness of the ISMS.
Records of incident response: Records of information security events, including incident reports, conclusions of investigations, and steps taken to lessen the effects of incidents and stop them from happening again.
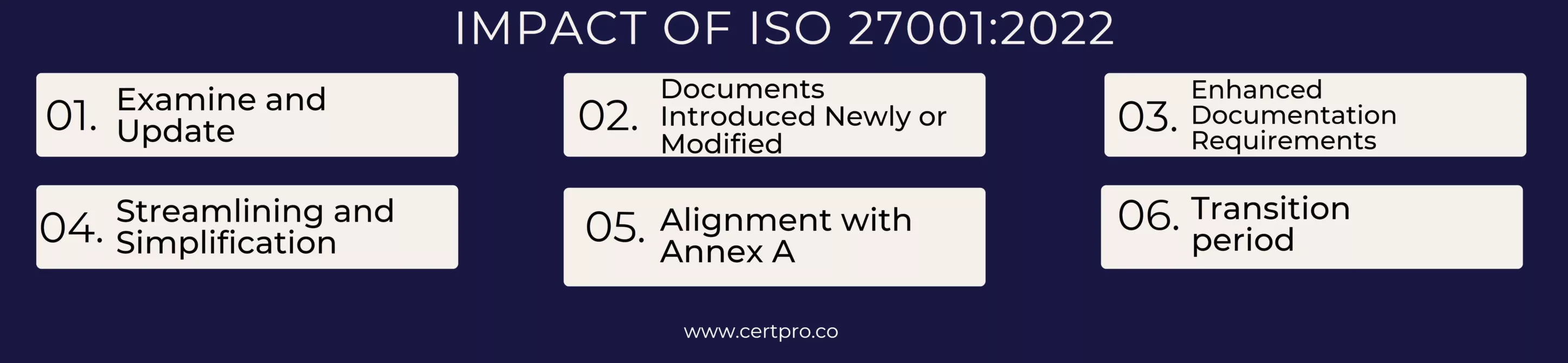
WHAT IS THE IMPACT OF THE ISO 27001:2022 REVISION ON MANDATORY DOCUMENTS AND RECORDS?
The ISO 27001 2022 revision makes updates and adjustments to the requirements of the standard, which have an effect on the obligatory papers and records. Here are some broad points to keep in mind, even if the precise adjustments may vary:
Examine and Update: In light of the updated ISO 27001 standards, organizations must examine their current obligatory documentation and records. This entails determining any gaps or regions that need to be modified in order to comply with the new standard.
Documents Introduced Newly or Modified: The revision may call for the addition of new, mandatory documents or the revision of already existing ones. The documentation for an organization’s information security management system (ISMS) should make sure to include any newly necessary papers.
Enhanced Documentation Requirements: The amended standard could give some parts of documentation more prominence. To demonstrate compliance with certain standards, organizations could be required to submit more information or proof in their records.
Streamlining and simplification: The adjustment may be made to make the documentation requirements more efficient and straightforward. This can entail cutting back on the number of required papers or changing their formatting to make them clearer and easier to understand.
Alignment with Annex A: The 2022 version may make modifications to Annex A, which contains a summary of the control goals and controls. Organizations must thus check their Statement of Applicability (SoA) and related documents to make sure they accurately represent the most recent control needs.
Transition period: Organizations that have previously achieved ISO 27001 required documents will probably have a transition period to modify their paperwork in order to comply with the new standards. It is crucial to remain up-to-date on any transitional instructions given by the accreditation or certification agencies.
WHAT ARE THE MANDATORY DOCUMENTS OF ISO 27001?
The ISO 27001 clauses outline the essential components of a cybersecurity plan that a corporation must document to pass an audit and achieve compliance. A commonly used collection of six configurations effectively covers all ISO 27001 clauses, even though there isn’t an official list of required documents.
1. Scope of the ISMS Document: The departments and assets your plan aims to safeguard from cyberattacks are listed in the ISMS Scope Document, which is a concise document. This inventory of susceptible components determines the extent of the all-encompassing security strategy and is an essential first step.
2. Information Security Policy: Senior management is in charge of creating a comprehensive security policy that is customized to the particular requirements and business processes of their particular company. Concrete proof that all organizational levels are aware of and adhering to the recommended processes must support this policy.
It is imperative to take the time necessary to ensure that this policy is complete, detailed, and robust, as clients and partners may seek to study and evaluate it. Give priority to accurate facts and provide clearly understood, concrete steps instead of relying solely on ambiguous assurances. Companies should provide this policy to all staff members, along with planned training sessions that clarify each step and reinforce safety precautions.
3. Risk Assessment and Methods: The risk assessment and methodology report is one of the most research-intensive of the ISO 27001 required documents. This report lists the possible security threats that are particular to a company and rates the relative threat of each risk that is found.
Most importantly, this paper needs to explain the process used to evaluate each risk. For example, when assessing a risk related to company-issued laptops, important variables, including the number of laptops in use, the kind of laptops, and the security configurations on each laptop, are crucial components to consider.
4. The Application’s Statement: The applicability of the 114 extra security measures included in ISO 27001’s Annex A varies based on the types of companies. For example, one of the requirements in Annex A is that IT personnel have Non-Disclosure Agreements (NDAs); nevertheless, this may not apply to firms that do not have IT personnel assigned to them.
The Statement of Applicability is a document that specifies and explains which Annex A requirements apply and are included in the final paperwork, as well as which ones do not. There should be proof to back up every decision taken in this regard. An organization’s successful response to the security issues associated with each Annex A control that has been determined to be applicable to it must be described in a report that corresponds with the control.
5. Plan for Risk Treatment: An organization’s strategy for reducing risks that were found during the risk assessment is described in this document. It complies with ISO 27001 by offering four approved risk mitigation strategies: changing, avoiding, sharing, or keeping the risk. It emphasizes particularly precise plans for high-priority issues. Completing this risk treatment plan helps auditors evaluate compliance and effectiveness while strengthening security procedures. For these preparations to guarantee a strong reaction to possible security risks, specificity is essential.
6. List of Security Objectives: This section lists an organization’s cybersecurity objectives in relation to the previously established risk assessment and remediation procedures. Before compiling the necessary ISO 27001 documentation, many firms may already have existing goals, and it is best to include both current projects and future ambitions.
These objectives should be concrete and measurable, with an emphasis on practical advantages rather than just administrative aspects. Auditors will look for evidence of active pursuit of these aims as well as tangible outcomes. For example, if the goal is to maintain a dependable cloud service, giving data on the service’s total uptime and downtime is critical. Another measurable goal may be for employees to recognize and report phishing emails to security personnel.
HOW MANY MANDATORY CLAUSES ARE THERE IN ISO 27001?
ISO 27001 comprises two sections: Mandatory Clauses and Annex A Controls.
1. Mandatory Clauses: The first part of the ISO 27001 standard comprises 11 clauses (0–10), of which clauses 4–10 are the ones that a business needs to specifically execute in order to comply with ISO 27001 standards.
2. Annex A Controls: The latest ISO 27001 version includes 93 security controls from which an organization can develop its security risk assessment.
WHAT ARE THE CONSEQUENCES OF MISSING ISO 27001 MANDATORY DOCUMENTS?
An auditor carefully records major and minor non-conformities and areas that could be improved upon during an audit for ISO 27001 certification. An essential component of a significant non-conformity is the lack of ISO 27001 mandatory documents.
A significant non-conformity occurs when important, required documents are not completed to the required level. These non-conformities can impede the certification procedure, necessitating a thorough examination and reexamination of the precise documentation requirements. You must obtain or recreate the required proof to address the missing pieces and fix these problems. The information is then cataloged and sent to the auditor for a thorough examination in the following phase. An extension of your timeline, usually lasting one to four weeks, may result from this procedure, depending on how long it takes to gather and present the evidence.
Get a professional help from CertPro
Organizations must create and maintain a number of necessary documents that serve as the cornerstone of a successful information security management system in order to achieve ISO 27001 compliance. These papers provide the framework required to identify, assess, and manage information security threats. Organizations may profit from CertPro’s experience as a trusted partner in ISO 27001 compliance throughout the certification process. In order to help firms adopt and maintain the ISO 27001 required documents and ensure a successful route towards ISO 27001 certification documentation, CertPro offers extensive assistance, advice, and auditing services. Organizations may improve their information security posture and win the trust of their stakeholders by working with CertPro to protect sensitive data and precious assets.
FAQ
What information must the ISMS documentation have?
How many provisions of ISO 27001 need to be followed?
The two components of ISO 27001 are organized separately. 11 clauses make up the first and most important section, from clause 0 to clause 10. The foundation for your Statement of Applicability (SoA), comprising 114 controls, is provided in the second portion, Annex A.
What are the six ISO-required procedures?
What are the requirements for passing ISO 27001?
Who conducts audits of ISO 27001?
Auditors who are qualified and impartial must conduct audits in accordance with ISO 27001. It is often necessary for the auditor to demonstrate competence for an ISO 27001 audit by having a proven understanding of the standard and auditing best practices.

About the Author
SUBBAIAH KU
Subbaiah Ku is the Regional Director for CertPro in Oman, bringing a wealth of expertise in process and system auditing. As a seasoned lead assessor, Subbaiah is dedicated to ensuring the highest standards in compliance and security. His unique blend of technical acumen, rooted in Mechanical Engineering, is complemented by a diverse range of certifications and extensive training.
IS SOC 2 THE SAME AS ISO 27001?
In today's digital landscape, ensuring the safeguarding of client data is paramount for businesses. Adhering to recognized compliance standards is vital to meeting this demand. ISO 27001 vs. SOC 2 represent two prominent benchmarks in the realm of data security with...
WHO NEEDS ISO 27001 CERTIFICATION AND WHY?
The esteemed ISO 27001 security framework is designed to evaluate the effectiveness of an organization's Information Security Management System (ISMS) in safeguarding its data. Obtaining ISO 27001 certification is a practical way for a corporation to demonstrate its...
IS ISO 27001 RISK ASSESSMENT VITAL FOR SECURITY MEASURES?
The ISO 27001 standard provides a framework for information security, highlighting the importance of a thorough risk assessment procedure. Organizations use the methodical and complex ISO 27001 risk assessment process to identify and assess information security...




