In an era where data breaches and cyber threats are increasingly prevalent, organizations must prioritize the security of their information assets. An ISO 27001 internal audit is when you conduct an audit internally within the organization to assess whether your information security management system (ISMS) satisfies the ISO 27001 standard. Conducting internal audits is crucial to ensuring that an organization’s information security management system (ISMS) complies with the standards of the ISO 27001 standard. An internal ISO 27001 audit is a methodical, unbiased examination of an organization’s ISMS to confirm compliance with the ISO 27001 standard. Utilizing an ISO 27001 internal audit template can streamline this process by providing a structured framework for conducting the audit effectively and efficiently.
In this article, we delve into what is ISO 27001 audit entails, how to audit ISO 27001, and the key steps involved in conducting one. Additionally, we discuss the frequency of internal audits, the procedural steps to carry out an audit effectively, and the process of concluding an audit.
WHAT IS AN ISO 27001 INTERNAL AUDIT?
WHY TO UNDERGO AN INTERNAL AUDIT?
HOW DO I CONDUCT AN ISO 27001 INTERNAL AUDIT?
CHECKLIST OF ISO 27001 FOR INTERNAL AUDITS?
BENEFITS OF ISO 27001 INTERNAL AUDITS
WHO CAN CONDUCT AN INTERNAL AUDIT?
ISO 27001 INTERNAL AUDIT REPORT SAMPLE
HOW SHOULD AN ISO 27001 INTERNAL AUDIT REPORT BE WRITTEN?
GETTING PROFESSIONAL HELP IN CONDUCTING AN ISO 27001 INTERNAL AUDIT
What is an ISO 27001 internal audit?
An ISO 27001 internal audit, also known as an ISO 27001 audit, is a systematic and independent examination of an organization’s Information Security Management System (ISMS) to assess its conformity with the requirements of the ISO/IEC 27001 standard. The standards for performing an internal audit of an organization’s ISMS are outlined in clause 9.2 of the ISO/IEC 27001 standard. The provision states that qualified, impartial, independent auditors who are free from conflicts of interest must conduct internal audits at predetermined intervals.
During the internal audit, auditors review documentation, interview personnel, and observe processes to gather evidence on the implementation and effectiveness of the ISMS. They analyze how well the ISMS complies with the standard’s standards as well as the organization’s own rules and goals, and whether the controls, policies, and procedures defined in the ISMS are being followed consistently.
The internal audit ISO 27001 process follows established guidelines and standards for the audit’s scope, frequency, and techniques. The audit must include suggestions for remedial and preventive measures, as well as the identification of non-conformities and potential for improvement. The findings, recommendations, and any action taken must be recorded.
By following these guidelines, an organization can ensure that its internal audit ISO 27001 are successful in assessing the sufficiency and efficacy of its ISMS and pinpointing chances for improvement. This aids the firm in maintaining the confidentiality, precision, and availability of its information assets and in meeting ISO/IEC 27001 regulations.
Why to undergo an internal audit?
Any business that wishes to keep up an efficient information security management system (ISMS) and abide by the ISO 27001 standard must conduct an internal audit. Here are some explanations for why a company ought to do an internal audit:
Ensure ISO 27001 compliance: An internal audit assists a company in evaluating the ISO 27001 standard’s requirements against its ISMS. This guarantees that the firm is in compliance with the standards and can prove its dedication to information security.
Gaps and weaknesses can be found. An internal audit can find ISMS gaps and weaknesses that may not have been known before. This enables the company to fill these gaps and develop its ISMS by taking corrective and preventative measures.
Ensure constant progress: By highlighting areas for improvement and offering suggestions for increasing an organization’s information security posture, an internal audit aids in the ongoing improvement of an ISMS.
Satisfying stakeholder and customer expectations: Customers and stakeholders want businesses to secure their sensitive data with effective information security procedures. An internal audit enables a company to show that it is serious about information security and dedicated to safeguarding the data of its stakeholders and consumers.
Preparing for external audits: An internal audit helps a company prepare for external audits by identifying areas that auditors may examine. This, in turn, reduces the likelihood of non-conformities being found during an external audit by allowing the business to address any potential issues beforehand.
A business may ensure the efficiency of its ISMS and show its dedication to information security by conducting an internal audit. It helps to discover opportunities for development and provide insightful information about the organization’s information security posture.
HOW SHOULD AN ISO 27001 INTERNAL AUDIT REPORT BE WRITTEN?
One of the main focuses of ISO 27001 is comprehensive documentation. As a result, you should anticipate that your internal audit report will cover everything in detail. The following are certain components to look at in your report:
Overview: The management team will be reviewing the internal audit report, so keep that in mind. As a result, it is crucial to include a succinct synopsis that makes it easier for readers to quickly and easily understand the report.
Planning the Audit: In this section, we will describe the auditor’s objectives, provide the auditor’s qualifications, and include any relevant details such as names and addresses.
Findings: All relevant observations regarding the Information Security Management System (ISMS) are included in this section.
Categorization of Results: The results will be divided into three categories in this section: chances for improvement, minor nonconformities, and major nonconformities, if relevant.
Suggestions: To close control gaps or improve overall resilience, this section outlines ideas and an action plan that map ISMS clauses and controls.
Scheduled Remediation: A timeline for filling in any gaps and other shortcomings found will be included in the audit report.
CHECKLIST OF ISO 27001 FOR INTERNAL AUDITS?
1. Form an internal team: Building an effective internal resource team is essential to managing your company’s compliance process and leading the certification audit. Important figures, including function leaders, the security officer, IT heads, and people operations, among other pertinent staff, should be on this skilled team.
This committed group will be essential to the Information Security Management System (ISMS) during all of its design, construction, and monitoring phases. Their extensive participation places them in a strategic position to respond to inquiries made by outside auditors throughout the certification audit. This team guarantees an all-encompassing approach to ISMS deployment, ensuring a comprehensive understanding and efficient management of security standards inside the business by merging experience from several functional areas.
2. Coordinate the ISMS Plan and Scope: Work with department heads to ensure that the ISO 27001 certification’s scope is in line. Analyze the scope of data, goods, procedures, services, systems, roles, affiliates, and locations that are essential for security using the ISMS. Verify that the scope sufficiently encompasses all data that needs to be protected. Analyze internal audit findings in this area and incorporate suggested improvements.
3. Examine Documentation: Read through all of the ISO 27001 documents, such as the Information Security Policy, Risk Treatment Plan, and Statement of Applicability, in detail. Verify that management has reviewed and approved each document. Furthermore, make sure that all policies are well documented and that the company intranet is accessible to all employees.
4. Establishing Proof: Ensure that a methodical process for gathering evidence exists, leaving a trace of papers and records that confirm compliance with ISO standard standards. This entails recording several policies, such as the data backup policy, business continuity management policy, vendor risk management policy, change management policy, vulnerability management policy, and data retention policy, among others. Make sure that all employees have access to these written policies on the corporate intranet.
5. Integrate Internal Audit Insights: Examine the internal audit report with care, taking note of any findings, suggestions, and remedial measures that are made. Understand that your internal audit report is a crucial record that is frequently one of the major items that external auditors look for while doing the primary audit.
By following this ISO 27001 internal audit checklist, organizations can ensure a thorough examination of their Information Security Management System (ISMS) to validate compliance with ISO 27001 standards.
BENEFITS OF ISO 27001 INTERNAL AUDITS
Protecting the data and assets of your company is crucial in the modern digital environment. Internal weaknesses can also be a major concern, even though external threats like cyberattacks are always present. This is where internal audits, like ISO 27001 audits, become your go-to tool for strengthening and fortifying your firm.
Proactive Problem Solving: Uncover nonconformities before others discover them: Internal audits, including ISO 27001 audits, act as a proactive measure, identifying weaknesses in your systems and processes before they escalate into major issues. This allows you to address potential problems and prevent costly breaches or disruptions.
Improved Accountability and Transparency: Show your dedication to management and let them know it. Frequent internal audits show investors and management how committed you are to data protection and information security. This openness promotes confidence in your company’s capacity to handle sensitive information with care.
Constant Improvement: Educate yourself about Constant Improvement: Internal audits, such as ISO 27001 audits, highlight areas for improvement and offer insightful information on how well your current controls are working. You may use this data to constantly improve your overall security posture, add new controls, and hone your security strategy.
WHO CAN CONDUCT AN INTERNAL AUDIT?
The ability to conduct internal audits for ISO 27001 conformity offers flexibility through the utilization of internal workers, independent third-party auditors, or ISO 27001 consulting firms. Accredited external auditors are not required for these internal evaluations, in contrast to certification audits.
Choosing an internal auditor with objectivity and impartiality is essential to the process. It is best to steer clear of conflicts of interest by making sure the selected person did not oversee the controls that are being examined or had any involvement in the creation of the Information Security Management System (ISMS). This precaution has a logical justification: it is difficult to remain impartial when evaluating one’s own work. Therefore, to guarantee a comprehensive and objective assessment, choose a resource knowledgeable in auditing practices and the ISO standard. For further insights into conducting ISO 27001 internal audits, consider reviewing an “ISO 27001 2013 Internal Audit Report” to understand the format and content typically included in such reports.
ISO 27001 Internal Audit Report Sample
Organizations can evaluate their security controls, identify vulnerabilities, and improve their overall information security posture by following the key steps outlined in this article, which include thorough planning, conducting comprehensive audits, documenting findings, and putting corrective actions into place. Internal audits for ISO 27001 provide several advantages, from risk reduction to assurance of compliance to ongoing improvement. These audits, whether carried out internally or with the aid of external auditors, are crucial for protecting sensitive data, fostering stakeholder confidence, and upholding compliance with global standards. Organizations may proactively repair security holes and safeguard their crucial assets in an ever-evolving environment by prioritizing internal audits. Additionally, referring to an “ISO 27001 Internal Audit Report Sample” can offer practical insights into the audit process and facilitate effective implementation of security measures.
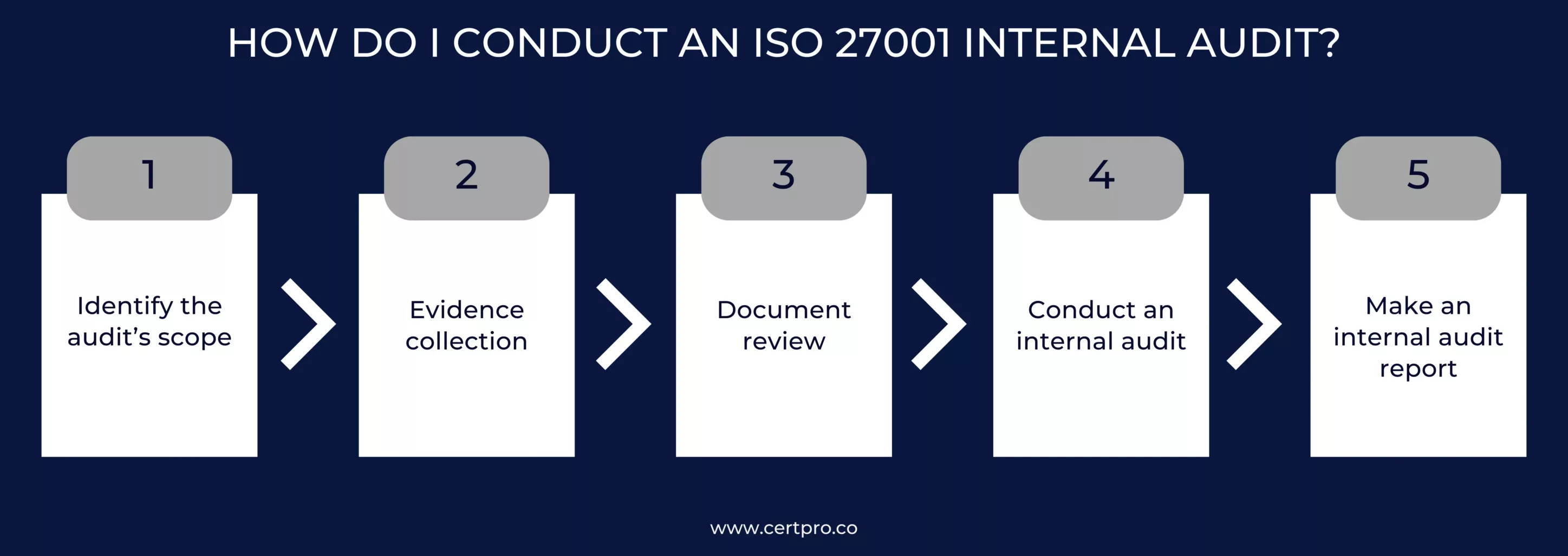
How do I conduct an ISO 27001 Internal audit?
Identify the audit’s scope: The first step should be to select the processes, policies, procedures, and controls for the ISMS that will be audited. Determine the pertinent paperwork and the individuals in charge of each area. You should definitely know which ISO 27001 clauses and Annex A are similar and relevant to your certification, and then you have to choose an audit team that has the expertise, training, and experience required to carry out the audit.
Evidence collection: The auditor will gather evidence during an internal audit to back up their findings and judgments. Records, logs, and other material that shows how the organization’s ISMS is being used and maintained can be included in this proof.
The process for collecting evidence could include:
- Examining guidelines and regulations to make sure they are being followed.
- Interviewing staff members to determine their roles and responsibilities
- Examining system logs and access control records to confirm the security of the organization’s information assets
- Examining physical security measures to make sure they are implemented and working as planned
- Checking training records to make sure that staff members are getting the right information security policies and procedures training
Document review: Examining the organization’s policies, practices, and other paperwork to make sure they adhere to the standards of the ISO 27001 standard is known as document review. The auditor will check the company’s documentation to make sure it appropriately reflects the information security processes of the business and is full, current, and up-to-date.
During the document review process, there might be:
- Examining the organization’s information security guidelines to make sure they adhere to ISO 27001
- Examining the paperwork for the organization’s risk assessment and risk management to make sure it is complete and efficient
- Examining the asset inventory of the company to confirm that all information assets have been recognized and categorized
- Checking incident management records to make sure issues are being recognized, reported, and handled properly
- Examining the organization’s business continuity and disaster recovery documentation to make sure it is ready for significant catastrophes or disasters
Conduct an internal audit: It’s now time for the internal auditor to start their evaluation. They will examine supporting materials and controls, speak with control owners in interviews, and see operational processes in action. All of this information will help the auditor determine if your organization’s goals are being attained and are in compliance with ISO 27001. They can use it to find any holes that need to be filled before the subsequent certification audit.
Make an internal audit report: An internal audit will produce a report, just like an external audit report. The internal auditor summarizes their findings in this section, which should cover any non-conformities and action items. The internal audit report must incorporate the following components:
- Introduction: The introduction should provide a brief overview of the audit objectives, scope, and methodology.
- Executive summary: This should provide a high-level summary of the audit findings and conclusions. It should highlight any major strengths and weaknesses during the audit and provide an overall assessment of the organization’s ISMS.
- Audit findings: It should provide a detailed description of the findings and conclusions of the audit. The audit criteria should serve as the organizing principle for this section, which should also include both positive and negative findings.
- Non-conformities: This section should identify any instance, such as where the organization is not meeting ISO 27001 internal audit requirements. Each non-conformity should be clearly identified and include a description of non-conformity.
- Annexes: Any further supporting material or proof that corroborates the audit findings and recommendations should be included in the annexes. Copies of the policies, processes, and other paperwork that were evaluated during the audit may be included in this.
Organizations can evaluate their security controls, identify vulnerabilities, and improve their overall information security posture by following the key steps outlined in this article, which include thorough planning, conducting comprehensive audits, documenting findings, and putting corrective actions into place. Internal audits for ISO 27001 provide several advantages, from risk reduction to assurance of compliance to ongoing improvement. These audits, whether carried out internally or with the aid of external auditors, are crucial for protecting sensitive data, fostering stakeholder confidence, and upholding compliance with global standards. Organizations may proactively repair security holes and safeguard their crucial assets in an ever-evolving environment by prioritizing internal audits.
Getting professional help in conducting an ISO 27001 Internal audit
To guarantee the efficiency and compliance of their ISMS, firms must conduct an internal ISO 27001 audit. Organizations may successfully carry out internal audits that pinpoint strengths, flaws, and opportunities for growth by following the guidelines presented in this article. Additionally, firms may save time, increase the accuracy of their audits, and guarantee compliance with ISO 27001 requirements by streamlining the internal audit process using CertPro. Organizations may enhance their internal audits using CertPro while maintaining a robust and efficient ISMS.
FAQ
How should I prepare for an internal ISO 27001 audit?
Choosing the audit team, establishing the audit goals, developing an audit schedule, and identifying the required resources are all steps in the planning process for an internal ISO 27001 audit.
How frequently should an internal ISO 27001 audit be performed?
A variety of factors, including business size, complexity, and risk profile, may affect how frequently ISO 27001 internal audits are conducted. Internal audits should, however, be performed on a regular basis, such as annually or biannually.
Is it possible for me to perform an internal ISO 27001 audit myself, or should I contact a third party?
According to ISO 27001, an organization’s own staff can conduct internal audits as long as they have the necessary independence and expertise. However, given their objectivity and competence, many firms opt to work with external auditors. The choice is based on the organization’s resources, knowledge, and particular needs.
Why is it essential to perform an internal ISO 27001 audit?
Carrying out an internal ISO 27001 audit may assist firms in evaluating the efficiency of existing information security measures, spotting gaps in security, and ensuring conformance to the standard.Carrying out an internal ISO 27001 audit may assist firms in evaluating the efficiency of existing information security measures, spotting gaps in security, and ensuring conformance to the standard.
What are the essential steps in carrying out an internal ISO 27001 audit?
The planning, execution, documentation, findings, communication, and implementation of remedial measures are the essential phases in an ISO 27001 internal audit.

About the Author
ANUPAM SAHA
Anupam Saha, an accomplished Audit Team Leader, possesses expertise in implementing and managing standards across diverse domains. Serving as an ISO 27001 Lead Auditor, Anupam spearheads the establishment and optimization of robust information security frameworks.
IS SOC 2 THE SAME AS ISO 27001?
In today's digital landscape, ensuring the safeguarding of client data is paramount for businesses. Adhering to recognized compliance standards is vital to meeting this demand. ISO 27001 vs. SOC 2 represent two prominent benchmarks in the realm of data security with...
WHO NEEDS ISO 27001 CERTIFICATION AND WHY?
The esteemed ISO 27001 security framework is designed to evaluate the effectiveness of an organization's Information Security Management System (ISMS) in safeguarding its data. Obtaining ISO 27001 certification is a practical way for a corporation to demonstrate its...
IS ISO 27001 RISK ASSESSMENT VITAL FOR SECURITY MEASURES?
The ISO 27001 standard provides a framework for information security, highlighting the importance of a thorough risk assessment procedure. Organizations use the methodical and complex ISO 27001 risk assessment process to identify and assess information security...




