Choosing the right SOC 2 audit firm is a critical decision for organizations seeking to demonstrate their commitment to data security and compliance. It evaluates the efficacy of internal controls for security, availability, processing integrity, confidentiality, and privacy inside a service company. The audit’s results provide valuable assurance to clients and stakeholders that their data is handled with the utmost care and security. However, navigating the sea of available options and understanding the nuances of each audit firm’s capabilities can be a daunting task.
This article examines the crucial elements to take into account when picking the best SOC 2 audit company, such as competence and experience, knowledge of the industry, compliance understanding, flexibility, communication, and post-audit assistance.
WHAT IS SOC 2 AUDIT AND ITS TYPES?
A SOC 2 (Service Organization Control 2) audit is a comprehensive examination of a service organization’s controls related to security, availability, processing integrity, confidentiality, and privacy. The audit is conducted by an independent third-party CPA (Certified Public Accountant) firm to assess whether the organization’s internal controls meet the criteria set by the American Institute of CPAs (AICPA).
These are designed to provide assurance to clients, stakeholders, and business partners that the service organization has implemented appropriate controls to protect sensitive data and maintain the highest level of service quality.
Service organization control audit fall into two categories:
- SOC 2 Type I Audit: The SOC 2 Type I audit assesses the design of a service organization’s controls at a specific point in time. The audit evaluates whether the controls are suitably designed to meet the Trust Services Criteria (TSC) for security, availability, processing integrity, confidentiality, and privacy.
- SOC 2 Type II Audit:The SOC 2 Type II audit goes beyond the Type I audit and assesses both the design and operating effectiveness of controls over a specific period, typically six months to one year. This audit provides a more comprehensive evaluation of how well the controls are functioning to achieve their intended objectives.
Both types of audits play a crucial role in demonstrating a service organization’s commitment to data security, availability, processing integrity, confidentiality, and privacy.
AUDIT STANDARDS OF SOC 2
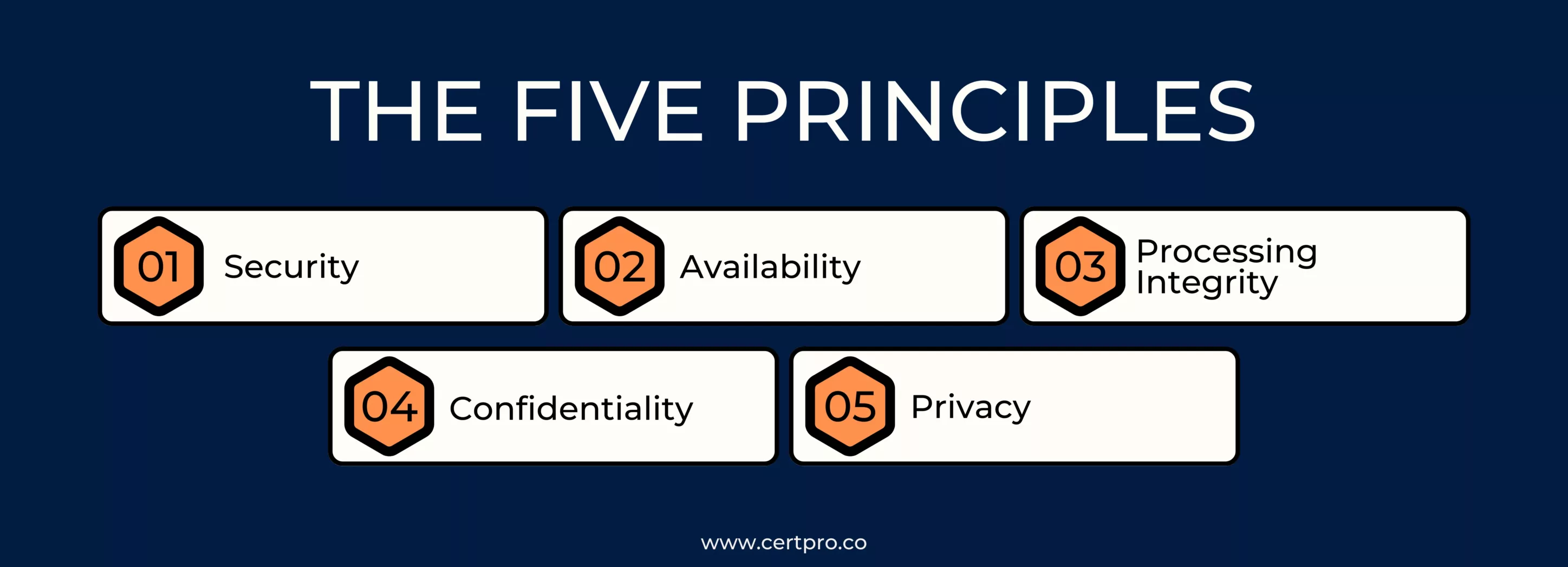
The five principles are:
1. Security: The Security principle is concerned with preventing unauthorized access, use, or disclosure of system resources. It evaluates the effectiveness of the organization’s security measures to safeguard sensitive data and prevent security breaches.
2. Availability: The Availability principle assesses the availability of the system, ensuring that it is accessible and operational for authorized users. This includes measures to prevent and respond to system interruptions and minimize downtime due to technical or operational issues.
3. Processing Integrity: The Processing Integrity principle evaluates the accuracy, completeness, and validity of data processing. It focuses on the reliability of system processing and the integrity of data throughout its lifecycle.
4. Confidentiality: The Confidentiality principle concentrates on the protection of sensitive information from unauthorized access or disclosure.
5. Privacy: The Privacy principle centers on the organization’s handling of personally identifiable information (PII) and compliance with relevant privacy regulations and agreements.
During the SOC 2 audit standards, the auditor evaluates the service organization’s controls and processes against these Trust Services Criteria to assess their effectiveness in meeting the stated objectives.
THINGS TO CONSIDER BEFORE HIRING A SOC 2 AUDIT FIRM
A company’s data security, compliance initiatives, and general corporate reputation can all be adversely impacted by choosing the wrong SOC 2 (System and Organization Controls) auditor. A company should take these factors into consideration before hiring an audit firm.
1. Reputation and Experience: Look for an auditing company that has a good track record of performing service organization control audit. Verify their track record and experience evaluating businesses of similar size, industry, and complexity as yours. A company’s track record of successful audits serves as evidence of its competence and dependability.
2. Member of the AICPA: Make sure the audit company is a member of the American Institute of CPAs (AICPA) and that its auditors possess the necessary certificates and credentials. Auditors who are qualified have the knowledge and training needed to perform complete and accurate SOC 2 audits.
3. Business knowledge: Take into account an audit company that is experienced in and knowledgeable about your particular business and regulatory standards. The auditors’ ability to modify the assessment in accordance with industry-specific risks and difficulties.
4. Scope of services: Clarify the scope of services provided by the audit firm in addition to the Audit of service organization control. Some businesses might offer extra cybersecurity and compliance services that fit your organization’s demands, thereby saving you time and resources.
5. Audit approach and methodology: Inquire about the audit firm’s approach and technique for carrying out the SOC 2 examination. You will have a better understanding of what to anticipate throughout the audit and how the company handles possible problems if the procedure is clear-cut and transparent.
6. Client references: Ask the audit firm for client testimonials and references if you want to learn more about their previous clients’ experiences. To find out more about the firm’s responsiveness, communication, and audit quality overall, get in touch with these references.
7. Cost and Budget Considerations: Obtain comprehensive pricing data and assess the SOC 2 audit’s cost in light of the benefits received. To achieve a fair and cost-effective engagement, balance the pricing with the caliber of the services being delivered.
When choosing a SOC 2 audit company, you should carefully take into account these criteria and exercise due diligence. By doing so, you can create a successful partnership that will not only help you reach compliance but also improve the data security and credibility of your organization in the eyes of your stakeholders.

GET EXPERT ASSISTANCE FOR HOW TO CHOOSE THE RIGHT SOC 2 AUDIT FIRM
By partnering with CertPro, organizations can rest assured that their commitment to data security and compliance will be upheld with the utmost integrity and professionalism.
FAQ
HOW IMPORTANT IS TO CHOOSE THE RIGHT SOC 2 AUDIT FIRM?
Choosing the right audit firm is crucial as it impacts the effectiveness of the SOC 2 assessment, data security, and compliance.
WHAT SHOULD I CONSIDER WHEN SELECTING AN AUDIT FIRM?
Consider their expertise, experience, industry knowledge, compliance understanding, and range of services offered.
HOW DOES INDUSTRY KNOWLEDGE PLAY A ROLE?
Industry-specific regulations and security challenges require an audit firm familiar with your sector for a tailored approach.
CAN AN AUDIT FIRM CUSTOMIZE THE PROCESS?
Yes, flexibility is essential, as a one-size-fits-all approach may not suit your organization’s unique needs.
HOW CAN I ASSESS THE FIRM REPUTATION?
Check reviews, testimonials, and client references to gauge their credibility and service quality.

About the Author
SUBBAIAH KU
Subbaiah Ku is the Regional Director for CertPro in Oman, bringing a wealth of expertise in process and system auditing. As a seasoned lead assessor, Subbaiah is dedicated to ensuring the highest standards in compliance and security. His unique blend of technical acumen, rooted in Mechanical Engineering, is complemented by a diverse range of certifications and extensive training.
HOW CAN STARTUPS ATTAIN SOC 2 COMPLIANCE IN 2024?
Trust is crucial for startups to do well in today's digital world. It's vital for establishing credibility with clients, especially in a data-driven environment where privacy is the main component. Therefore, getting a SOC 2 compliance report is crucial to building...
SOC TOOLS: How They Impact On Security Aspect Of The Organization
The changing cybersecurity landscape increases the importance of Security Operations Center (SOC) tools. Hence, it is essential for strengthening digital defenses and protecting against cyberattacks. SOC tools help security teams detect, monitor, and prevent security...
WHAT IS SOC FOR CYBERSECURITY?
In today's fast-paced digital landscape, ensuring robust cybersecurity measures is imperative for organizations aiming to protect sensitive data and maintain stakeholder trust. The American Institute of CPAs (AICPA) crafted the SOC for cybersecurity reporting...




