A major data breach has shaken India, revealing the personal information of 81.5 million people on the dark web. Passport details, Aadhaar numbers, phone numbers, addresses, and other sensitive information are all included in this hack and are being sold on underground online marketplaces. An entity known as “pwn001” first disclosed the hack, raising serious concerns about data security and potential consequences. Security professionals have confirmed the validity of this frightening Aadhaar card data leak, but the how and why behind it remain unknown.
Initial suspicions point to a third-party data leak, with clues that a company selling SIM cards could be the source. Other elements that may have played a role include undisclosed database vulnerabilities, weak security procedures, insider threats, and external hazards. When exchanging sensitive data with other parties, this incident highlights the critical importance of tight security measures, oversight, and regular security assessments. It underlines the importance of independent cybersecurity assessments in protecting people’s personal information and data integrity. This paper investigates the potential reasons and effects of this large data leak, shedding light on this vital issue.
HOW DID THE BIG BREACH OF AADHAAR DATA OCCUR?
The personal data of around 81.5 crore Indian residents has surfaced on the dark web, creating an alarming situation. This data dump includes sensitive information such as names, phone numbers, addresses, Aadhaar numbers, and passport information, all of which are for sale. The obvious concerns are: how did this large data breach occur, and how did the criminal gain access to such highly personal information about millions of people? What are the likely consequences of this significant data breach? ETBFSI gathered ideas from cybersecurity experts in order to shed light on these vital issues, and here are some potential causes for this troubling data leak.
An individual using the username “pwn001” triggered the discovery of this alleged major Aadhaar card data leak by posting this alarming revelation on a dark web forum, disclosing the personal information of 81.5 crore Indians. According to Security, a US-based cybersecurity firm, this data contains names, phone numbers, addresses, Aadhaar details, and passport information, all of which are for sale. The key concern here is how the hacker was able to infiltrate and obtain access to such a massive library of safe and private information belonging to millions of Indian residents. What caused this breach, and what are the potential consequences for the people and organizations affected?
While the actual nature of this breach is unknown, initial suspicions point to a potential third-party data leak. The hacker, who goes by the username “pwn001,” has published example spreadsheets that indicate the breach may have come from a third-party firm involved in selling SIM cards to clients. Srinivasa Rao, a partner in Nangia and Co.’s Risk Advisory Services, emphasizes this potential. Other causes that contributed to this significant data breach include unknown database vulnerabilities, a lack of database security fortification, insider threats, and risks originating from other parties.
This incident underscores the critical importance of implementing stringent security governance practices and oversight when sharing sensitive data with external third parties and partners. To safeguard the personal information of citizens, organizations must prioritize robust security measures and continuous monitoring, both within their systems through regular Information Security and Cyber Security Audits and throughout their network of partners and vendors. Rao also recommends seeking independent cybersecurity reviews from agencies that do not have vendor relationships with the organization to ensure a comprehensive assessment of security measures.
CURRENT SITUATION OVERVIEW
On October 9, a user known as ‘pwn0001’ raised the danger of a huge security risk by publishing a topic on Breach Forums in which they offered access to a massive database comprising records of 81.5 crore “Indian citizen Aadhaar and passport” details. To put this in context, India’s total population exceeds 1.486 billion people, according to a blog post by a US-based cybersecurity business. They said that their HUNTER (HUMINT) unit detectives made contact with this threat actor and discovered that he was offering to sell the complete Aadhaar and Indian passport databases for a whopping USD 80,000.
The hacker known as “pwn001” discovered this breach, and the Central Bureau of Investigation (CBI) is actively investigating it. This event adds to India’s rising anxiety about data security. Notably, a recent social media post disclosed that unknown hackers have released personal information from over 800 million Indians, including names, fathers’ names, phone numbers, passport numbers, Aadhaar numbers, and ages.
Furthermore, the government launched an investigation into a Aadhaar data breach affecting the CoWin website in June. This hack allegedly exposed the personal information of vaccinated persons, including prominent individuals, raising concerns about the security of sensitive information in the digital age.
HOW AADHAAR DATA CAN BE MISUSED
The Unique Identification Authority of India (UIDAI) assigns an Aadhaar number to each Aadhaar card. These cards include sensitive biometric information such as fingerprints, iris scans, and facial photographs in addition to the unique identifier.
As data privacy and security issues grow, it is critical to protect this personal information. The prospect of malicious actors misusing the biometric details contained in the Aadhaar card is a major worry since they can use them to participate in unauthorized authentication and potentially commit fraudulent acts. In an era when preserving personal information is more important than ever, it is critical for individuals to remain attentive and take the required safeguards to ensure the security and privacy of their Aadhaar data.
HOW DO YOU DETERMINE IF AADHAAR IS BEING MISAPPLIED?
For those living in India, the Aadhaar card is an indispensable identity document that includes vital biometric data such as a fingerprint, retinal scan, and photo. The Aadhaar card is linked to numerous services, including bank accounts and mobile numbers, through the use of this biometric information. For enhanced convenience, Aadhaar may now be securely used for financial transactions thanks to the launch of the Aadhaar-enabled Payment System (AePS). To avoid any potential abuse or unauthorized access to this private Aadhaar data, security measures must be given top priority. This is especially crucial in light of recent worries about Aadhaar data leak.
To safeguard your Aadhaar biometrics, you can follow these steps online:
- Visit the official UIDAI website at resident.uidai.net.in/biometric-lock.
- Provide your Aadhaar number and the security code.
- Click ‘Send OTP,’ and you will receive a verification code on your registered mobile number.
- Enter the code and click ‘Verify.’
- On the subsequent page, select ‘Enable Biometric Locking’ and then click ‘Enable.’ If you ever wish to unlock your biometrics, you can revisit the mentioned website and choose ‘Disable Biometric Locking.’ These precautions help ensure the security and privacy of your Aadhaar biometric data.
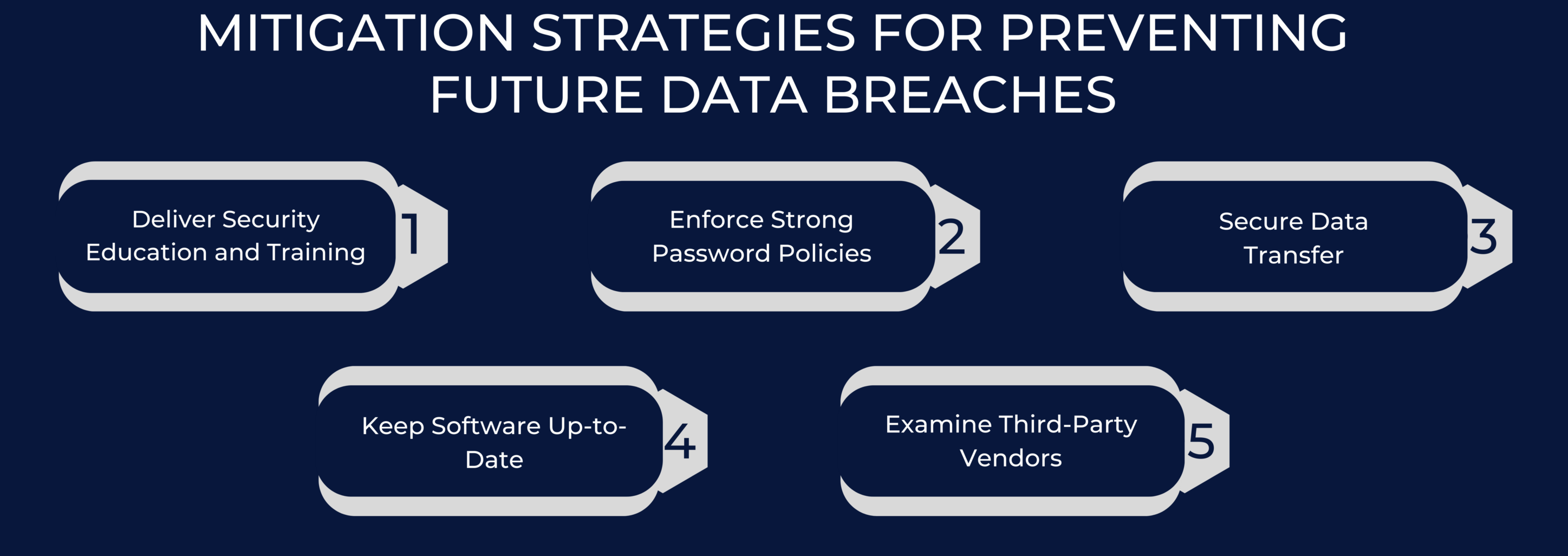
MITIGATION STRATEGIES FOR PREVENTING FUTURE DATA BREACHES
Deliver Security Education and Training: Educating the workforce on ransomware and malware risks is vital for safeguarding organizations. Understanding threat operations and precautions is crucial to preventing data breaches. A spear-phishing attack on 300 U.S. universities in 2018 resulted in a significant data loss, highlighting the importance of user education and training in preventing such incidents.
Enforce Strong Password Policies: Strong passwords are your first line of defense against illegal access. Users should prevent password sharing and avoid using the same password across many systems, which is a hazardous practice. For added security, use a combination of upper and lower case letters, numbers, and special characters in your passwords.
Secure Data Transfer: Control data transfers between devices to reduce the danger of data getting into the wrong hands. For secure data transfers, secure transmission techniques and encrypted channels should be employed. Unencrypted networks allow hostile users to intercept or monitor data, resulting in unlawful access.
Keep Software Up-to-Date: To reduce security vulnerabilities, keep software up-to-date. Cybercriminals can easily use outdated software with known issues and coding problems. To protect your systems from hacking, you need to regularly update and maintain your software.
Examine Third-Party Vendors:Boost security with third-party providers, confirm their strict security protocols, and put intrusion prevention systems (IPS) in place for continuous threat detection and real-time monitoring to protect against Aadhaar data leaks.
WHAT HAPPENS IF AADHAAR CARD DATA IS LEAKED?
India’s unique identifying system, Aadhaar, generates a 12-digit identity number for each person based on their biometric information and demographics. There are serious hazards associated with Aadhaar data leaks, including the possibility of Aadhaar card data leaks, identity theft, and financial fraud. Malicious actions like creating bank accounts or asking for loans using stolen information can result from unauthorized access. People are susceptible to targeted cybercrimes like phishing emails and fake calls since Aadhaar data is sensitive.
Because Aadhaar is connected to so many government programs, there is a greater chance of fraudulent access, which might prevent legitimate recipients from receiving services. A significant hack might undermine public confidence in the Aadhaar system and the organizations in charge of running it, posing questions about security and dependability in general.
Authorities must put strong security measures in place, update processes frequently, and react quickly to breaches in order to mitigate these dangers. People should report unusual activity, update their Aadhaar details on a regular basis, and remain alert. Legal and regulatory frameworks are essential for guaranteeing the privacy of individuals and holding companies responsible for data breaches, such as those involving Aadhaar card data leaks. It is crucial to respond quickly to Aadhaar card data leaks in order to minimize risks, protect the identity system, and keep the public’s confidence in this essential infrastructure.
AADHAAR LEGAL ISSUES AND PRIVACY CONCERNS
A lack of strong legislative backing and political resistance initially hampered the Aadhaar initiative. When oil corporations campaigned for mandatory Aadhaar connections to bank accounts for gas subsidy customers in 2012, legal difficulties arose. In 2013, the Supreme Court decided against this obligation, noting that the lack of an Aadhaar card should not prevent access to critical services. The Lok Sabha’s approval of the ‘Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits, and Services) Act, 2016’ provided critical legislative support. Following that, the NDA advocated for mandatory Aadhaar integration in services such as crop insurance, IT returns, SIM card acquisition, and automobile registrations.
Concerns about privacy, like the Aadhaar data breach and so many others, became a major issue, with the NDA claiming that privacy was not a fundamental right. The Supreme Court’s August 2017 decision, on the other hand, established privacy as a basic right under the Indian Constitution.
In 2018, the Supreme Court made history by issuing a landmark decision upholding the constitutionality of the Aadhaar initiative. This landmark decision had far-reaching effects since it allowed Aadhaar to be connected to tax returns and government aid programs, so eliminating the need for separate SIM cards and bank accounts. It also struck down controversial Section 57 of the Aadhaar Act, which had allowed companies and people to demand Aadhaar for a variety of services. Furthermore, the court stressed the necessity of protecting against possible Aadhaar data leaks by pressing the central government to swiftly enact strong data protection regulations.
However, despite these significant changes, several opponents argued that the court’s rulings did not fully address worries about the possible misuse of Aadhaar and the data it collects by the government. Regarding the Aadhaar data leak, it is apparent that concerns are still present. Ultimately, the Aadhaar saga sheds light on the complex interactions between legal, political, and privacy concerns in the digital age and provides insightful information about how identification and data protection are changing in India.

About the Author
GANESH S
Ganesh S, an expert in writing content on compliance, auditing, and cybersecurity, holds a Bachelor of Arts (BA) in Journalism and Mass Communication. With a keen eye for detail and a knack for clear communication, Ganesh excels in producing informative and engaging content in the fields of compliance, auditing, and cybersecurity, with particular expertise in ISO 27001, GDPR, SOC 2, HIPAA, and CE Mark.
JPMorgan Chase Discovers Data Breach Exposing Personal Info of Nearly Half a Million Customers
Excerpt from DailyHodl Article, Published on May 10, 2024 JPMorgan Chase, one of the leading banking institutions, has disclosed a significant data breach affecting approximately 451,809 customers, where personal information was compromised. According to recent...
Dell Acknowledges Data Breach: Customer Information Compromised
Excerpt from News18 Article, Published on May 10, 2024 Dell Technologies has confirmed a data breach, acknowledging that certain customers' names and physical addresses were exposed in the incident. The revelation came via an email sent to customers, which quickly...
LockBit Ransomware Mastermind Unveiled: Russian Hacker Dmitry Khoroshev Identified
Excerpt from The Hacker News Article, Published on May 07, 2024 The U.K. National Crime Agency (NCA) has identified Dmitry Yuryevich Khoroshev, a 31-year-old Russian national, as the mastermind behind the infamous LockBit ransomware operation. Khoroshev, also known by...