The protection of sensitive information has become critical for businesses and organizations in today’s digital age. With the rising frequency and sophistication of cyber threats, it is critical to implement strong security measures to safeguard critical data. ISO 27001, an internationally recognized standard for information security management, is crucial in assisting enterprises in protecting their information assets. The ISO 27001 compliance report, which acts as complete documentation of an organization’s adherence to the standard’s criteria, is an important part of ISO 27001 implementation. This article seeks to provide a detailed overview of ISO 27001 reports, their significance, and how businesses can develop and use them efficiently.
ISO 27001 is a framework for establishing, implementing, maintaining, and continuously improving an information security management system (ISMS) within the context of an organization, developed and maintained by the ISO and IEC, which stand for International Organization for Standardization and International Electrotechnical Commission, respectively. The standard outlines a risk-based approach to managing information security and includes a wide range of controls and practices aimed at protecting the information’s confidentiality, integrity, and availability.
WHAT IS THE ISO 27001 COMPLIANCE REPORT?
An ISO 27001 report is a detailed document that describes an organization’s compliance with the ISO/IEC 27001 standard for information security management systems (ISMS). This internationally acknowledged standard establishes, implements, maintains, and continuously improves an organization’s ISMS.
The compliance report is an important record of the organization’s dedication to information security. It usually includes information about the ISMS’s scope and context, the results of risk assessments and treatment plans, the implementation of security controls, documentation and records management, training and awareness initiatives, incident response and management procedures, performance monitoring and improvement processes, and ISO 27001.
This report is not only an internal document, but it is also an important tool for demonstrating ISO 27001 compliance to external stakeholders such as clients, partners, regulators, and auditors. It contributes to the development of trust, openness, and accountability in information security processes, as well as to ongoing efforts to protect sensitive data and mitigate security threats.
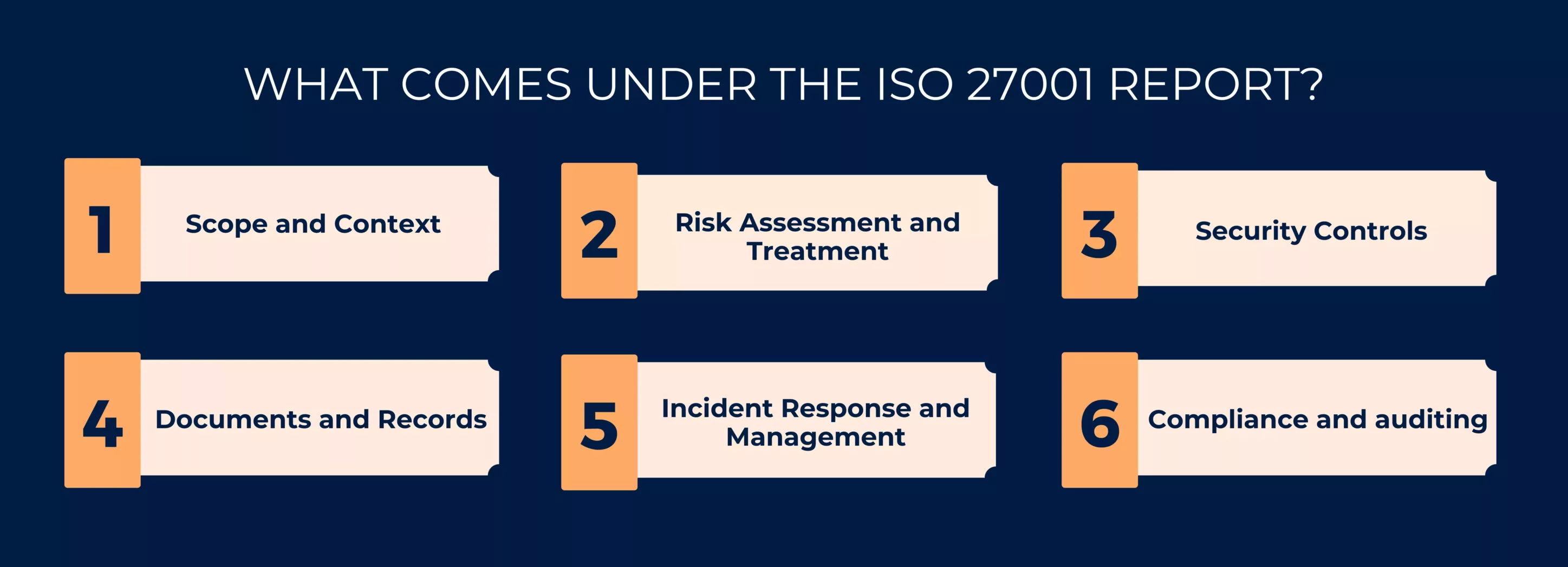
WHAT COMES UNDER THE ISO 27001 REPORT?
The Compliance report includes a number of critical components that demonstrate an organization’s conformity with the ISO/IEC 27001 standard for information security management systems (ISMS). These elements usually include:
- Scope and Context: Defining the ISMS’s scope, defining the limits of the organization’s information systems, and identifying the assets to be safeguarded.
- Risk Assessment and Treatment: Describe the organization’s risk assessment methodology, identify potential threats and vulnerabilities, and give a risk treatment plan outlining selected security controls and risk mitigation techniques.
- Security Controls: A description of the security controls applied within the organization, based on Annex A of ISO 27001, including areas such as access control, cryptography, physical security, and more.
- Documents and Records: Explaining the organization’s processes for developing, maintaining, and keeping documents, such as information security policies, procedures, guidelines, and records.
- Incident Response and Management: Outlining incident response protocols, including incident reporting, analysis, and resolution.
- Compliance and auditing: Explain how the organization achieves ISO 27001 compliance and how internal and external audits are undertaken to assess ISMS effectiveness.
All of them, taken together, present a full picture of an organization’s commitment to information security and compliance with ISO 27001 requirements. The compliance report is an important instrument for promoting transparency, trust, and responsibility in information security practices.
ISO 27001 COMPLIANCE REPORT SECTIONS
An ISO 27001 Report is a critical document that offers a thorough assessment of an organization’s ISO 27001 compliance with its information security management system (ISMS). This standard specifies the best practices for handling and safeguarding sensitive information inside an organization. The report is normally divided into five sections:
Examine Metadata:
The purpose of this part is to introduce the compliance report and provide important contextual information about the scope and objectives of the compliance assessment.
Contents: Information such as the assessment date, the entity being assessed (e.g., the organization or a specific department), the names and responsibilities of personnel involved in the assessment, and any additional regulations or standards being addressed in addition to ISO 27001.
Vulnerabilities:
This section’s purpose is to identify and categorize vulnerabilities in the organization’s information security management system. Vulnerabilities are flaws or gaps in security that could be exploited.
Contents: It includes a list of individual vulnerabilities uncovered during the assessment, as well as their severity levels, possible impact on security, and affected systems or processes. Each vulnerability should be given a distinct identifier for future reference.
Names and descriptions of vulnerabilities:
The purpose of this section is to go into the intricacies of each vulnerability found throughout the assessment, providing a more in-depth understanding of the concerns and their possible impact.
Contents: Detailed information for each vulnerability, such as the name or identifier, a description of the vulnerability, the affected systems or assets, the risk assessment (including likelihood and impact), recommended remediation steps, and the party or team responsible for addressing the issue.
Show/Hide Scan Details:
This section provides extra, more technical information for individuals who need a more in-depth grasp of the evaluation process.
Contents: It may contain thorough technical reports, scan methodology, vulnerability assessment tools, and any other important technical documentation.
HOW DO YOU CREATE A SUCCESSFUL ISO 27001 COMPLIANCE REPORT?
The ISO 27001 reports are critical in a variety of domains, including information security, quality management, and regulatory compliance. These reports are used to demonstrate an organization’s compliance with specified standards, rules, or best practices. Several fundamental concepts and best practices should be followed when preparing an effective compliance report to ensure accuracy, transparency, and usefulness. Let’s check out the five factors needed to create an effective ISO 27001 Report:
Thorough Documentation: Thorough documentation is required. The report should accurately capture every aspect of the organization’s ISMS installation and information security policies.
- Clear Language: In the report, use clear and simple language. Avoid using jargon or technical phrases that could be confusing to non-technical stakeholders.
- Visual Aids: Visual aids such as flowcharts, diagrams, and tables can help simplify complicated information and increase the readability of the report.
- Cross-Reference: To demonstrate compliance with the standard’s requirements, cross-reference the report with relevant sections of ISO 27001 compliance.
- Updates on a regular basis: The compliance report is not a static document. It should be evaluated and updated on a regular basis to reflect changes in the organization’s information security procedures as well as the developing threat landscape.
STREAMLINING ISO 27001 COMPLIANCE AND REPORTING WITH CERTPRO
CertPro is your reliable partner in achieving ISO 27001 compliance and streamlining the process of preparing ISO 27001 compliance reports. We provide a complete evaluation framework to assist you in evaluating your organization’s ISO 27001 compliance.
CertPro offers a customized path for ISO 27001 compliance. It enables you to prioritize activities, distribute resources efficiently, and ensure a smooth path to certification. We automate the documentation process, producing the policies, procedures, and records needed for ISO 27001 reports. This function saves time while also ensuring uniformity. provides real-time monitoring of your ISMS, allowing you to track progress, check security controls, and analyze compliance performance.
CertPro makes ISO 27001 reporting easier. It generates detailed reports on risk assessments, security control implementation, incident response, and other topics. We enable enterprises to become ISO 27001 compliant with ease, from the first evaluation to rigorous reporting. It’s a useful tool for achieving and maintaining compliance while also improving information security policies.
FAQ
How often should ISO 27001 compliance reports be updated?
Those compliance reports should be reviewed and updated on a regular basis to reflect changes in the organization’s information security processes as well as the ever-changing threat landscape. The frequency may vary depending on the demands of the organization and changes in conditions.
Who are the main consumers of compliance reports?
Internal stakeholders, external auditors, regulatory agencies, clients, partners, and anyone else interested in analyzing the organization’s commitment to information security are the major recipients of compliance reports.
Why is ISO 27001 compliance critical?
Compliance with ISO 27001 is critical for protecting sensitive information, retaining customer trust, meeting legal and regulatory obligations, and mitigating cybersecurity threats. It displays a dedication to excellence in information security.
How can businesses produce an effective report on their compliance with ISO 27001?
Organizations should provide thorough documentation, clarity, context, evidence, and suggestions when creating a successful compliance report. It should be rationally constructed and checked for accuracy on a regular basis.
What is the function of continuous improvement in ISO 27001?
ISO 27001 requires continuous improvement. Organizations should use data from monitoring and evaluation to identify areas for improvement and adjust their information security processes over time.
IS SOC 2 THE SAME AS ISO 27001?
In today's digital landscape, ensuring the safeguarding of client data is paramount for businesses. Adhering to recognized compliance standards is vital to meeting this demand. ISO 27001 vs. SOC 2 represent two prominent benchmarks in the realm of data security with...
WHO NEEDS ISO 27001 CERTIFICATION AND WHY?
The esteemed ISO 27001 security framework is designed to evaluate the effectiveness of an organization's Information Security Management System (ISMS) in safeguarding its data. Obtaining ISO 27001 certification is a practical way for a corporation to demonstrate its...
IS ISO 27001 RISK ASSESSMENT VITAL FOR SECURITY MEASURES?
The ISO 27001 standard provides a framework for information security, highlighting the importance of a thorough risk assessment procedure. Organizations use the methodical and complex ISO 27001 risk assessment process to identify and assess information security...




