Businesses are increasingly relying on information technology (IT) as a source of innovation, increased efficiency, and a competitive edge in the dynamic and always-evolving field of technology. Despite the advantages that accompany technological advancements, enterprises face significant risks. Threats to IT systems are numerous and include data leaks, cyberattacks, and system malfunctions. Organizations are depending more and more on IT risk management frameworks to help them navigate this complicated environment in response to these problems. The purpose of this blog article is to examine the fundamental ideas, importance, and components that make up IT risk management frameworks.
Organizations use IT risk management as a proactive approach to detect, assess, and reduce possible hazards related to their IT infrastructure. This strategy is essential since there are many different types of vulnerabilities that affect IT systems, and security breaches can have serious consequences. IT risk management frameworks are essential because they can safeguard sensitive data and expensive assets, keep corporate operations running smoothly by averting interruptions, and make regulatory compliance easier. Furthermore, by preventing financial and reputational damage from events like data breaches, such frameworks help to save costs.
WHAT IS IT RISK MANAGEMENT?
Organizations implement a proactive IT risk management approach to address possible vulnerabilities in their IT infrastructure in a methodical manner. This complete strategy includes several critical risk management framework steps to effectively identify, assess, and mitigate risks. Threats can originate from a variety of sources, including hostile activity, human error, software flaws, and hardware problems. Notably, hardware failures ranging from network outages to server troubles constitute a real threat to business continuity. Unresolved software bugs allow thieves to compromise system integrity and data security. Human errors, whether caused by carelessness or accidental mishaps, also significantly contribute to the risk landscape.
Organizations respond by following risk management framework examples and taking measured efforts to harden their IT infrastructure. This proactive strategy ensures the identification of potential threats as well as the execution of security solutions to establish a secure operational environment. Organizations that adhere to these risk management principles aim to protect their systems, data, and overall company operations from potential interruptions and harmful activity.
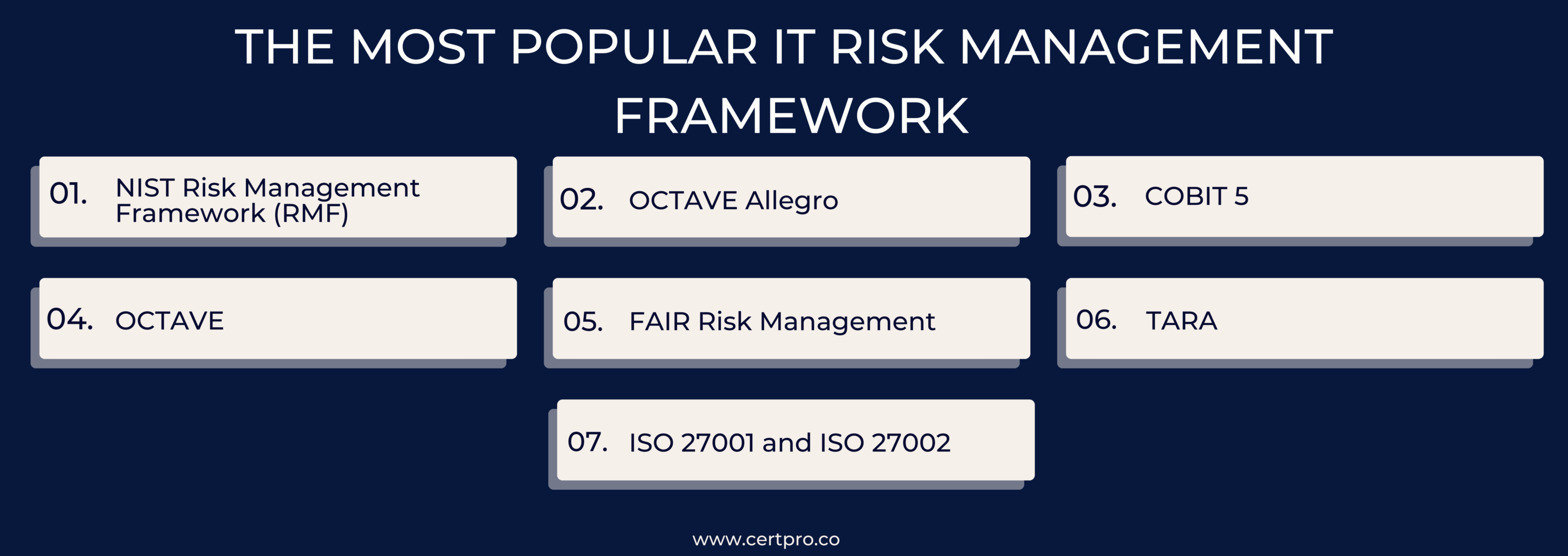
THE MOST POPULAR IT RISK MANAGEMENT FRAMEWORK
In the quickly changing world of information technology, competent risk management is essential for firms seeking to safeguard their assets and assure smooth operations. This discussion dives into several important IT risk management frameworks, clarifying specific techniques that respond to enterprises’ varying demands. The investigation includes discussions on risk management framework steps, which provide insight into the systematic principles included in these frameworks. Furthermore, relevant examples of risk management frameworks are provided, shedding light on the actual uses and efficacy of these techniques in handling the dynamic issues of today’s IT ecosystem.
1. NIST Risk Management Framework (RMF): Large firms with dedicated risk management resources might benefit from the organized approach of the National Institute of Standards and Technology’s RMF, a well-known framework for IT risk management. It is mostly qualitative, cybersecurity-focused, and particularly compliant with NIST SP 800-53 for federal government work. The NIST RMF is a seven-step process that helps businesses with planning, classification, control selection, implementation, authorization, evaluation, and ongoing monitoring. To assure security and privacy risk management, these processes entail actions including risk assessment, control deployment, and continuing evaluation. NIST RMF is especially helpful for companies that have risk management teams since it offers a thorough process for protecting data and systems.
2. OCTAVE Allegro: Carnegie Mellon University’s Software Engineering Institute introduced OCTAVE Allegro, a popular paradigm for IT risk management, in September 1999. Operationally Critical Threat, Asset, and Vulnerability Evaluation is an acronym that describes a simple approach that is appropriate for organizations with lone practitioners who are not experienced in risk management. It works well for smaller firms or those with a single practitioner, but it is not scalable for team-oriented approaches; therefore, it is not as suitable for companies that have teams dedicated to risk management. The use of ten forms for peer review by OCTAVE Allegro demonstrates its simplicity and allows for quick program deployment. This is especially useful for smaller firms that want to start their risk management program in a single day. Additionally, it uses fictitious risk scenarios as examples, such as threat trees. One drawback, though, is that it ignores ongoing governance concerns in favor of a static emphasis on a single moment in time.
3. COBIT 5: The Information Systems Audit and Control Association (ISACA) created the COBIT framework, which stands for Control Objectives for Information and Related Technology. The latest version of COBIT, version 5, was initially created with financial auditors in mind. It bridges the gap between technological challenges, business risks, and control requirements, benefiting businesses of all sizes. This all-inclusive framework makes it easier to effectively monitor and control IT resources, practices, and activities. Organizations can attain certain risk-related outcomes by implementing the critical procedures outlined in COBIT 5. These results include the creation of a risk management plan, a communication strategy, and the distribution of funds for risk assessment and mitigation.
4. OCTAVE: OCTAVE, or Operationally Critical Threat, Asset, and Vulnerability Evaluation, is a framework for risk management designed to help businesses identify, assess, and manage information security threats. OCTAVE has a complete approach, having originated in 1999 at Carnegie Mellon University’s Software Engineering Institute (SEI). It helps companies identify three critical information points: the organization’s most important information assets, possible dangers to these assets, and exploitable vulnerabilities. By combining these components, OCTAVE gives businesses the ability to identify information that may be dangerous, facilitating the development and use of strategies to reduce overall risk to their information assets.
5. FAIR Risk Management: Factors Analysis of Information Risk Management, or FAIR Risk Management, is the only quantitative IT risk management framework approach on this list. It gives practitioners a unique ability to express risk in monetary terms. FAIR has one unique advantage, nevertheless, in spite of its complexity in cost attributions to multiple factors, such as staff pay, telecommunications, and productivity. Monetary values can explicitly describe risks and controls. Experienced practitioners who are skilled at pricing every facet of a business find value in FAIR since it makes it possible to provide the board with hard data and expenses. The difficulty with FAIR, however, is that its complex implementation frequently necessitates significant resources, which limits its usability for firms lacking sufficient investment capacities.
6. TARA: MITRE’s systems security engineering processes include Threat Assessment and Remediation Analysis (TARA), which provides a thorough framework for identifying and assessing cyber vulnerabilities. The Threat Agent Library (TAL), Methods and Objectives Library (MOL), and Common Exposure Library (CEL) are the three primary parts of TARA. The six-step methodology entails detecting present risks, setting up a baseline, comprehending the goals and techniques of threat agents, figuring out exposures, and adjusting the information security strategy as necessary. TARA offers an organized method for evaluating and reducing threats in an organization’s information security environment, empowering them to proactively address cyber weaknesses.
7. ISO 27001 and ISO 27002: An internationally recognized resource for verifying an organization’s risk management and security capabilities is the ISO catalog. In the field of information security, ISO 27001 is a widely accepted standard that offers precise guidelines and controls for handling financial data, personnel information, intellectual property, and data entrusted to third parties. The basis for developing an Information Security Management System (ISMS) in an institution is ISO 27002, which is evolved from ISO/IEC 27001. It provides thorough explanations of the main controls from ISO 27001 together with the control goals that go along with them, making it easier to implement the controls in a variety of operational settings. All things considered, these ISO standards are essential to improving and certifying information security procedures worldwide.
HOW CAN A RISK MANAGEMENT FRAMEWORK BE IMPLEMENTED?
Creating an IT risk management framework necessitates a methodical approach to identifying, evaluating, mitigating, and overseeing organizational risks. This includes defining the scope, establishing objectives, and identifying stakeholders. Use a variety of tools, including brainstorming and historical data analysis, to identify potential risks and categorize them (e.g., strategic, operational). Use risk assessment tools to prioritize risks and implement risk mitigation techniques such as risk avoidance or reduction. Review, update, and share risk information on a regular basis, incorporating risk considerations into decision-making. Risk identification, assessment, and mitigation are examples of risk management framework steps, and tools such as risk matrices aid in the process.
1. Prepare Your Information Systems Efficiently: Build a solid framework by using knowledge from OMB policies and NIST publications. This procedure guarantees a simpler approach while optimizing the RMF implementation. Protecting vital assets is prioritized in accordance with security needs. This fundamental level lays the groundwork for complete protection by improving risk management’s efficacy and efficiency.
2. Effectively Sort Your Information Systems: Structure your IT systems in accordance with business objectives, budgetary plans, and sector-specific guidelines. Use the FIPS 199 guidelines from NIST to understand security classifications and identify possible threats. In order to provide a more robust information system design, this organizational model guarantees alignment with business objectives, improves security measures, and permits proactive risk assessment.
3. Choose the Right Security Measures with Confidence: Use the wide range of global security measures provided by NIST, making sure the controls you select align with the security requirements of your company. Streamline monitoring procedures by utilizing control mapping feature, which is essential for successfully reducing cyber risks. By using it strategically, you may strengthen your security architecture and provide a proactive defense against cyber attacks.
4. Effectively Put selected security controls into practice: Apply the approved security measures to your IT systems. If they function as expected and meet the required regulatory requirements, move on to the next phase. Implementing this deployment ensures that strong security protocols protect your information systems, enabling compliance with industry requirements and enhancing resilience against threats.
5. Evaluate Security Measures Well: After security measures have been first set up, evaluate their effectiveness on a regular basis to ensure that the requirements are being followed. Use human evaluations,an automation tool for compliance, to make sure security measures always satisfy legal standards. This continuous assessment preserves the integrity of your security architecture and offers a proactive method for maintaining compliance and fixing possible flaws.
6. Secure Senior Official Approval for Information Systems: Get top officials’ approval for the broad implementation of the IT risk management framework so that executives and stakeholders can participate in the decision-making process. By bringing organizational leadership and important stakeholders into alignment with the risk management initiative’s strategic objective, this collaborative method guarantees total support for the implementation.
7. Monitor and Review: Monitor and evaluate risk management plans on a regular basis to adjust to evolving conditions. Analyze present risks, find new ones, and determine how well the measures being used to treat them are working. This continuous process guarantees that plans are pertinent in light of prospective risk costs and that controls are in place to manage developing risks.
THE SIGNIFICANCE OF IT RISK MANAGEMENT SYSTEM
An IT risk management framework is an essential strategic tool to identify potential issues in an organization. This all-inclusive plan is essential for identifying current hazards and foreseeing potential future ones.
Take into consideration, for example, the critical requirement for a strong cybersecurity policy in an organization that maintains significant volumes of sensitive data on its computer systems, such as financial records and customer information. Without a clear framework for risk management, the following risks become more likely to affect the company:
1. Risk of Data Breach: Without a well-thought-out risk management plan, the business is more vulnerable to unwanted access and the possible disclosure of private information. This highlights how crucial it is to put in place a methodical approach to reduce the risks related to data breaches and illegal invasions.
2. Detriment to Reputation: Inadequate risk management procedures may lead to violations that harm the company’s brand and erode stakeholder and customer trust. This emphasizes how crucial effective risk management is to maintaining the company’s integrity and credibility in the eyes of its major stakeholders.
3. Financial Loss: Without a proactive risk management framework, the company faces the potential for financial losses incurred in addressing the aftermath of security breaches. This highlights the necessity of a strategic approach to risk management to minimize both the likelihood and impact of adverse financial consequences.
4. Legal Issues: Insufficient risk management raises the possibility that legal requirements won’t be followed, which could put the business in danger of difficulties and legal challenges. This emphasizes how important it is to have an efficient risk management system in place to make sure that regulations are followed and to reduce legal risks that could have a negative effect on the company.
5. Business Impact: Inadequate risk management plans can have a negative effect on productivity, continuity, and business operations. This highlights how important it is to have a clear risk management plan in place to protect the business’s overall ability to operate and its resilience in the face of unforeseen obstacles.
Essentially, having a clear IT risk management framework is like having an umbrella in case of unforeseen rain. It serves as a buffer, reducing possible risks and empowering the business to make wise decisions. In addition, if a business takes on too much risk without a solid plan, it could lose the trust of its stakeholders and suffer financial consequences.
FAQ
What is the primary purpose of an IT risk management framework?
An IT risk management framework serves as a proactive approach to detect, assess, and mitigate potential risks associated with an organization’s IT infrastructure. It helps safeguard sensitive data, ensure regulatory compliance, and prevent financial and reputational damage from security breaches.
Why do organizations need IT risk management frameworks?
IT risk management frameworks are essential for organizations to navigate the complex landscape of IT-related risks. They help identify vulnerabilities, ensure operational continuity, comply with regulations, and protect assets from threats like cyberattacks, data leaks, and system malfunctions.
What are the common sources of IT-related risks addressed by risk management frameworks?
IT risk management frameworks address risks arising from various sources, including hostile activities, human errors, software flaws, and device malfunctions. These frameworks proactively engage organizations in systematic methods to identify and mitigate weaknesses in their IT infrastructure.
How can organizations implement an IT risk management framework effectively?
Implementing an IT risk management framework effectively involves steps such as preparing information systems, aligning IT systems with business goals, selecting appropriate security measures and controls, obtaining senior official approval, and maintaining continuous monitoring and review for ongoing evaluation of security measures.
How does an IT risk management framework contribute to cybersecurity?
An IT risk management framework contributes to cybersecurity by identifying and mitigating potential risks associated with IT infrastructure. It aids in preventing data breaches, cyberattacks, and other security incidents, ultimately enhancing the overall security posture of an organization.

About the Author
SUBBAIAH KU
Subbaiah Ku is the Regional Director for CertPro in Oman, bringing a wealth of expertise in process and system auditing. As a seasoned lead assessor, Subbaiah is dedicated to ensuring the highest standards in compliance and security. His unique blend of technical acumen, rooted in Mechanical Engineering, is complemented by a diverse range of certifications and extensive training.
COMPLIANCE RISK MANAGEMENT: EXPERT STRATEGIES AND BEST PRACTICES
Compliance risk considers the organization's potential legal, material, and financial losses due to compliance failure. Thus, compliance risk is known as integrity risk. Organizations of all sizes are exposed to compliance risk. Hence, compliance failure results in...
TOP 7 DATA LOSS PREVENTION STRATEGIES IN 2024
In the contemporary business landscape, data is the cornerstone of organizational vitality. Businesses leverage data extensively to inform decisions, maintain competitiveness, and foster expansion. Nonetheless, they encounter multifaceted challenges emanating from...
TIPS FOR ARTICULATING YOUR SECURITY POSTURE TO STAKEHOLDERS
Cybersecurity is now a top-tier priority for any Organization. Data breaches can ruin the entire company, destroy customer trust, and damage reputation. However, companies can find decision-making difficulties because stakeholders, board members, department heads, and...




