In the ever-evolving landscape of data security and regulatory compliance, organizations are increasingly turning to innovative solutions to ensure the protection of sensitive information and build trust with their stakeholders. One such groundbreaking tool is SOC 2 compliance automation software. This software has emerged as a transformative force, reshaping the way businesses approach and achieve SOC 2 compliance.
Enter software, a technological marvel designed to streamline and optimize these complex compliance procedures. By leveraging advanced technologies like artificial intelligence and robotic process automation, this software empowers organizations to automate routine tasks, enhance accuracy, and ensure consistency across the compliance journey.
In this article, we will delve into the dynamic realm of SOC 2 compliance automation software, exploring its functionalities, benefits, and considerations. We will uncover how this innovative solution is revolutionizing the compliance landscape, enabling organizations to navigate the intricate web of data security requirements with unprecedented efficiency and confidence.
WHAT IS SOC 2 COMPLIANCE AUTOMATION?
It refers to the use of technology solutions to streamline and optimize the processes involved in achieving, maintaining, and demonstrating SOC 2 compliance. These solutions leverage automation, artificial intelligence (AI), machine learning (ML), and other advanced technologies to efficiently manage tasks such as risk assessment, control implementation, documentation, reporting, and monitoring, all of which are essential components of SOC 2 compliance.
Achieving this demonstrates an organization’s commitment to protecting sensitive information and ensuring that proper controls are in place.
SOC 2 compliance software helps organizations effectively manage and navigate the complex requirements of the Service Organization 2 framework while improving efficiency, accuracy, and transparency.
Key Features of SOC 2 Compliance Software:
- Control Mapping and Framework Alignment: It assists businesses in mapping their existing controls to the relevant service organization Control 2 trust principles, ensuring compliance with specific criteria for confidentiality, security, availability, processing integrity, and privacy.
- Automated Testing and Monitoring: These tools automate the testing of controls to ensure that they are operating effectively over time. It reduces the manual effort required for periodic assessments and provides real-time monitoring of control performance.
- Documentation management: It involves creating and maintaining comprehensive documentation. Software solutions provide a centralized platform for managing policies, procedures, risk assessments, evidence, and SOC 2 compliance audit trails.
- Risk Assessment and Mitigation: The software helps organizations identify and assess potential risks to data security and privacy. It enables the implementation of mitigation strategies to address vulnerabilities and threats.
- Workflow Customization: This software allows organizations to customize workflows and processes to their specific needs. This flexibility ensures that compliance efforts align with the organization’s structure and operational requirements.
In conclusion, This software plays a critical role in helping organizations efficiently achieve and maintain compliance with the Service Organization Control Framework.
BENEFITS OF SOC 2 COMPLIANCE AUTOMATION
It offers numerous benefits to organizations seeking to achieve and maintain compliance with the Service Organization Control 2 framework.
Some of the key benefits are:
1. Efficiency and Time Savings: Automation streamlines and accelerates the compliance process by reducing manual efforts and automating repetitive tasks.
2. Accuracy and Consistency: Automated processes ensure that controls are consistently applied and tests are executed accurately, minimizing the risk of human errors that can occur during manual procedures.
3. Real-Time Monitoring: Automation allows for continuous monitoring of controls, providing real-time insights into control effectiveness and identifying potential issues promptly.
4. Centralized Documentation: Compliance automation software provides a centralized repository for all compliance-related documentation, making it easier to manage, organize, and retrieve necessary information.
5. Audit Preparedness: Automated tools facilitate audit preparation by maintaining up-to-date documentation, evidence, and reports, enabling a smoother and more efficient audit process.
6. Consolidated Reporting: Automation generates comprehensive compliance reports, including Type 1 and Type 2 reports, in a consistent and standardized format, making it easier to communicate compliance status to stakeholders.
7. Risk Mitigation: Automated tools facilitate the identification and mitigation of risks, ensuring that controls are in place to safeguard sensitive data and prevent potential breaches.
8. Vendor Management: For organizations that rely on third-party vendors, automation can streamline the assessment and management of vendor compliance with Service Organization Control 2 requirements.
In summary, it provides organizations with a wide range of benefits, including increased efficiency, accuracy, real-time monitoring, and enhanced risk management. By leveraging automation tools, organizations can effectively manage their compliance obligations, reduce non-compliance risks, and demonstrate their commitment to data security and privacy to stakeholders and clients.

AUTOMATION TOOLS FOR SOC 2 COMPLIANCE
Automation tools play a crucial role in streamlining and enhancing these processes for organizations. These tools are designed to automate various aspects of compliance management, from documentation and control testing to monitoring and reporting.
Some key automation tools commonly used for compliance for Service Organization Control 2 are:
1. Compliance Management Software: Dedicated compliance management platforms provide a centralized hub for managing all compliance-related activities. These tools often include features such as policy and control documentation, risk assessment, task management, and audit tracking.
2. GRC (Governance, Risk, and Compliance) Platforms: GRC platforms offer comprehensive solutions for managing governance, risk, and compliance initiatives.
3. Automated Control Testing Tools: These tools automate the testing of controls outlined in the Service Organization Control 2 framework. They can simulate control scenarios, perform tests, and provide evidence of control effectiveness.
4. Continuous Monitoring Solutions: Continuous monitoring tools enable real-time monitoring of control effectiveness and compliance status. They can detect anomalies, deviations, or potential issues and provide alerts, allowing for immediate corrective action.
5. Document Management Systems: These systems automate the storage, organization, and retrieval of compliance-related documents. They often include version control, access management, and document approval workflows.
6. Audit Management Software: Automated audit management tools streamline the entire audit process, from planning and scheduling to evidence collection and reporting.
7. Security Information and Event Management (SIEM) Systems: SIEM systems automate the collection, analysis, and correlation of security-related events across an organization’s IT infrastructure.
8. Encryption and Data Protection Solutions: Automation can be applied to data protection measures, such as encryption and data masking, to ensure the confidentiality and privacy of sensitive information.
When selecting automation tools for Service Organization Control 2, organizations should consider factors such as ease of integration, scalability, vendor reputation, and alignment with their specific compliance needs.
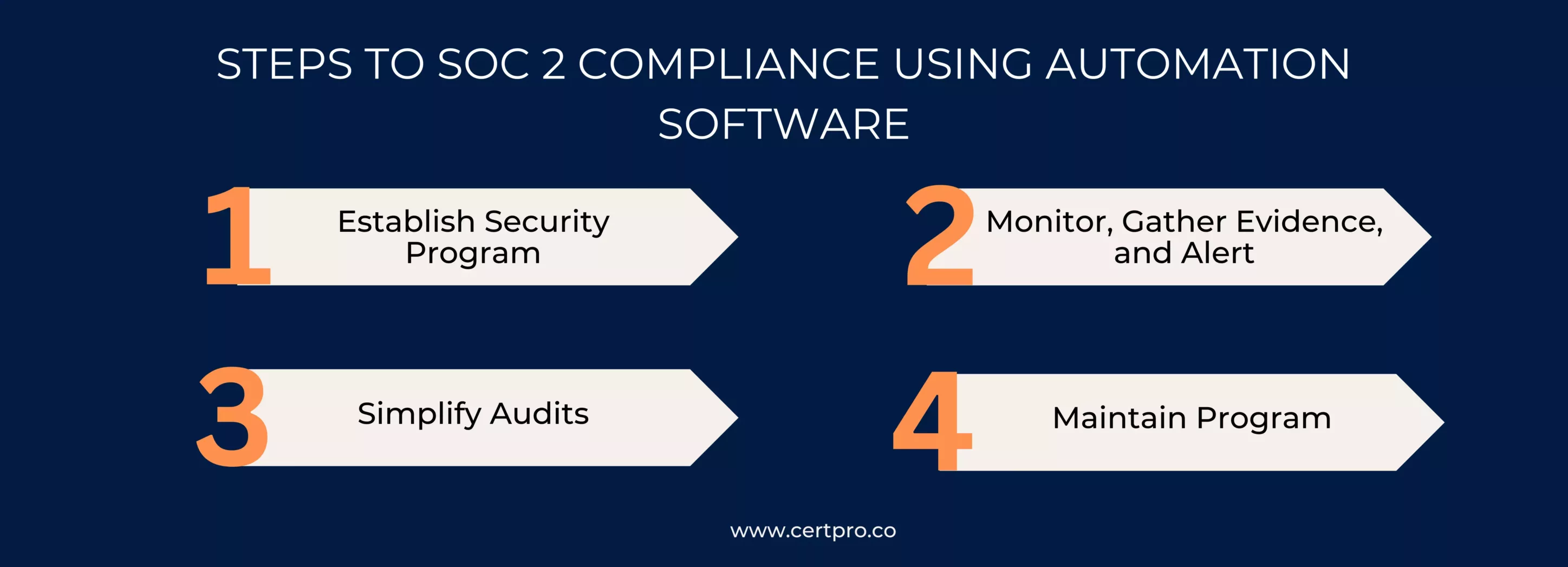
STEPS TO SOC 2 COMPLIANCE USING AUTOMATION SOFTWARE
Achieving this involves a series of steps to ensure that an organization’s controls and processes align with the Trust Services Criteria (TSC) established by the American Institute of Certified Public Accountants (AICPA). When utilizing automation software, these steps can be streamlined and made more efficient.
To achieve Service Organization Control 2 with Automation Software, the steps are as follows:
1. Establish Security Program: At this point, you should be considering security processes, encryption, firewalls, and other best practices that you want to implement. You’ll identify your company’s top risks and incorporate them into early decisions about processes and policies, what you’ll need to monitor, and when you’ll need alerts from your software.
2. Monitor,Gather Evidence, and Alert: Make sure you have automatic monitoring and evidence collection in place, and configure your alerts to notify you whenever compliance is jeopardized due to your specific behavior (or inactivity).
3. Simplify Audits: Use your SOC 2 compliance software reports and evidence library to simplify the Service Organization Control 2 audit process now that your security program is in place and your automation software is providing constant monitoring.
4. Maintain Program: No security program, no matter how amazing your automation software, is set-it-and-forget-it. Someone should be in charge. Check in on a frequent basis, keep an eye out for new developments (such as new privacy legislation in the markets you service), and update your automated software as needed.
Incorporating the compliance automation of Service Organization Control 2 into your organization’s processes can significantly enhance your ability to achieve and maintain Service Organization Control 2 compliance efficiently and effectively. It helps ensure that your controls are consistently implemented, monitored, and documented, providing assurance to clients, partners, and stakeholders about the security and privacy of your services.
EMBRACING THE FUTURE OF COMPLIANCE WITH SOC 2 AUTOMATION
In the realm of evolving data security and compliance, SOC 2 automation software emerges as a transformative tool, redefining how businesses approach and achieve compliance. It navigates the complex landscape of SOC 2 requirements, fostering efficiency, transparency, and trust. By centralizing documentation, automating tests, and enabling real-time monitoring, it offers unparalleled benefits: efficiency, accuracy, risk mitigation, and audit readiness. Embracing SOC 2 automation tools propels organizations towards effective compliance, securing sensitive data, and fortifying stakeholder confidence.
FAQ
WHAT IS SOC 2 COMPLIANCE AUTOMATION SOFTWARE?
This software streamlines the process of adhering to Service Organization Control 2 framework principles by automating tasks like data collection, control testing, and reporting.
WHAT IS THE FUNCTION OF SOC 2 COMPLIANCE AUTOMATION SOFTWARE?
The software integrates with systems, automates assessments, and offers real-time monitoring to enhance efficiency and accuracy.
HOW DOES IT AUDIT READINESS?
The software centralizes data, automates testing, and enhances monitoring, leading to smoother SOC 2 compliance audit preparations and processes.
IS SERVICE ORGANIZATION CONTROL 2 COMPLIANCE AUTOMATION SOFTWARE SUITABLE FOR CLOUD-BASED SYSTEMS?
Yes, this software can be deployed for on-premises systems as well as cloud-based environments. It offers flexibility and accessibility, making it suitable for organizations with cloud-hosted applications and services.
CAN COMPLIANCE AUTOMATION OF SOC 2 SOFTWARE REPLACE HUMAN INVOLVEMENT ENTIRELY?
While this software significantly reduces manual effort, it may not completely replace human involvement.

About the Author
SUBBAIAH KU
Subbaiah Ku is the Regional Director for CertPro in Oman, bringing a wealth of expertise in process and system auditing. As a seasoned lead assessor, Subbaiah is dedicated to ensuring the highest standards in compliance and security. His unique blend of technical acumen, rooted in Mechanical Engineering, is complemented by a diverse range of certifications and extensive training.
HOW CAN STARTUPS ATTAIN SOC 2 COMPLIANCE IN 2024?
Trust is crucial for startups to do well in today's digital world. It's vital for establishing credibility with clients, especially in a data-driven environment where privacy is the main component. Therefore, getting a SOC 2 compliance report is crucial to building...
SOC TOOLS: How They Impact On Security Aspect Of The Organization
The changing cybersecurity landscape increases the importance of Security Operations Center (SOC) tools. Hence, it is essential for strengthening digital defenses and protecting against cyberattacks. SOC tools help security teams detect, monitor, and prevent security...
WHAT IS SOC FOR CYBERSECURITY?
In today's fast-paced digital landscape, ensuring robust cybersecurity measures is imperative for organizations aiming to protect sensitive data and maintain stakeholder trust. The American Institute of CPAs (AICPA) crafted the SOC for cybersecurity reporting...