In our increasingly linked world, where data powers businesses, the importance of strong cybersecurity measures is obvious. It’s important to note that vulnerability management plays a crucial role in cybersecurity because flaws in networks, hardware, and software systems can compromise the safety of an organization. Newcomers are introduced to the fundamentals of this subject through our in-depth beginner’s guide. It gives you the knowledge you need to defend your business against prospective assaults. Vulnerability management is the proactive process of locating, evaluating, prioritizing, and fixing security problems in an organization’s IT infrastructure.
In order to increase your company’s security, cost-effectiveness, regulatory compliance, and reputation, it is crucial to keep your environment secure and eliminate risks. If one is to successfully address the always-evolving difficulties in cybersecurity, it is essential to master the tools, strategies, and best practices for managing vulnerabilities.
WHAT IS VULNERABILITY MANAGEMENT?
One important component of IT risk management is vulnerability management, which is the continuous assessment, ranking, and remediation of security flaws in an organization’s software and IT infrastructure.
Security vulnerabilities encompass design, operational, or implementation flaws in a network or networked asset that hackers could exploit for cyberattacks, gain unauthorized access, or undertake other harmful operations. Examples include unpatched vulnerabilities in an operating system’s remote desktop protocol that enable device takeover or firewall configuration errors that permit malware entrance. Because today’s enterprise networks are so large and dynamic, manual or ad hoc vulnerability management is practically impossible. To make the process more efficient, cybersecurity professionals use automated vulnerability management tools.
Continuous vulnerability management is acknowledged as a critical security control by the Center for Internet Security (CIS), which highlights the importance of this control in thwarting common assaults. With the help of this strategy, IT security professionals may strengthen defenses and proactively address vulnerabilities before they are exploited.
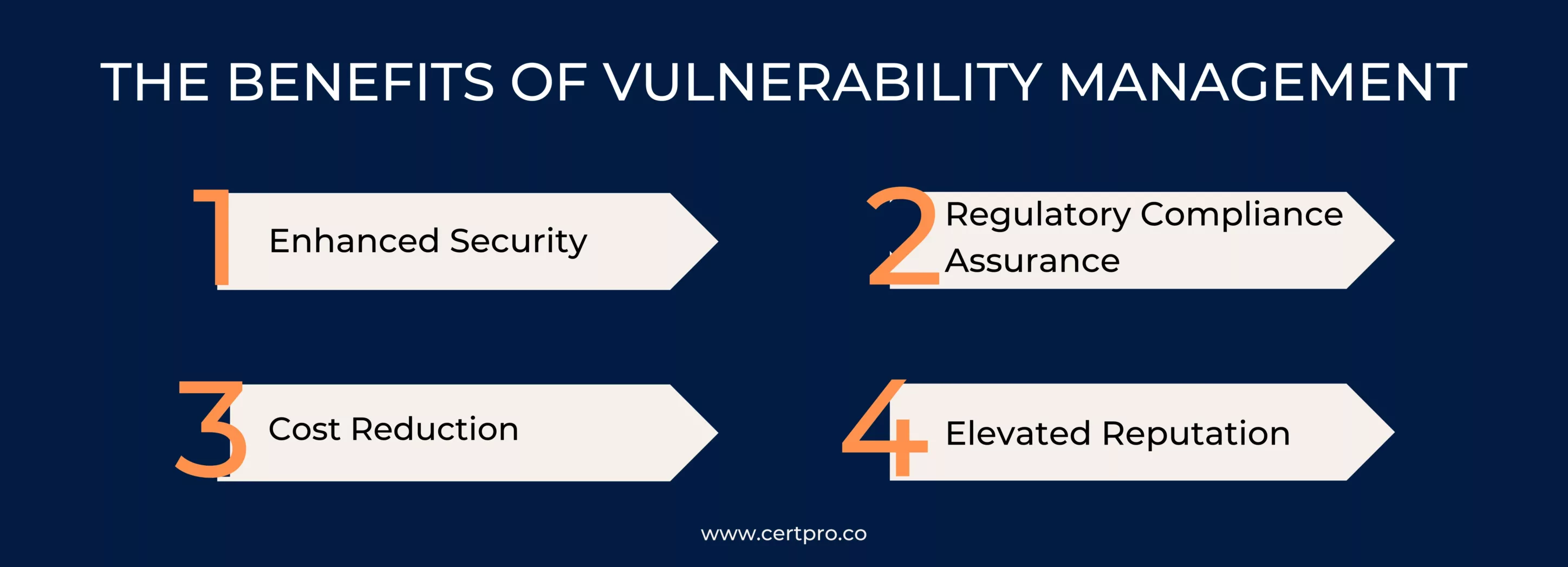
THE BENEFITS OF VULNERABILITY MANAGEMENT
An organization’s overall cybersecurity strategy heavily relies on vulnerability management, which offers numerous appealing benefits. Let’s explore the benefits of vulnerability management in more detail:
1. Enhanced Security: The management of vulnerabilities is a vital part of a strong security plan. Organizations strengthen their defenses by proactively identifying and fixing weaknesses. A crucial part of protecting sensitive assets and data, this proactive strategy significantly reduces the chance of security breaches and data breaches.
2. Regulatory Compliance Assurance: For a wide range of enterprises, strict cybersecurity regulations and compliance standards are applicable. Viability management enables organizations to comply with these regulatory and industry-specific requirements. Organizations demonstrate their commitment to compliance by meticulously managing vulnerabilities to make sure they adhere to regulations and avoid legal issues.
3. Cost Reduction: It is frequently more cost-effective to prevent security breaches rather than cope with their consequences. Businesses may identify and reduce potential risks thanks to the management of vulnerabilities before they turn into significant incidents. This preventative strategy lowers the expense of post-breach actions, such as legal fees, government fines, and reputational damage.
4. Elevated Reputation: It takes ongoing dedication to security and data protection to earn the trust of clients, partners, and stakeholders. Giving managing vulnerabilities top priority clearly shows a clear sign of a company’s dedication to data protection. Because of their dedication, they become more credible and have a better reputation in their respective industries, which also helps their contacts.
VULNERABILITY MANAGEMENT BEST PRACTICES
Adopting vulnerability management best practices not only integrates the process into cybersecurity activities but also enhances ROI by cultivating a culture of continuous improvement. By carefully implementing these best practices, you may create a culture that is resilient and collaborative while successfully protecting important assets from new risks. This strategy goes beyond simple deployment, building a dynamic environment that proactively fixes risks and adjusts to the always changing cybersecurity landscape. The descriptions of each of the suggested acts are as follows:
Staying Informed: Organizations may quickly respond to emerging risks by being informed about the most recent threats and vulnerabilities by subscribing to security news and alerts.
Regular Scanning: Regular vulnerability scans find flaws in software, networks, and systems as they appear, minimizing the window of opportunity for possible attackers.
Effective Prioritization: Organizations can prioritize vulnerabilities based on their seriousness, possible impact, and likelihood of exploitation, allowing them to focus first on the most important security threats.
Documentation:Maintaining clear and accurate records is critical for compliance and audits. In order to help with regulatory compliance and post-incident analysis, it acts as a historical record of activities, choices, and results.
Employee Training: Educating employees about the importance of cybersecurity and their role in detecting and reporting vulnerabilities enables them to be active contributors to the organization’s security. This encourages a culture that is concerned about security.
WHAT ARE THE 5 STEPS OF THE VULNERABILITY MANAGEMENT CYCLE?
The vulnerability management cycle consists of five primary stages, which are:
Step 1. Assess: Managing vulnerabilities well is essential to securing systems from online attacks. Vulnerabilities are similar to time bombs that hackers use to compromise system integrity and sensitive data. Making a detailed inventory of all of your assets—both virtual and physical—is a crucial first step in a strong vulnerability management program. This procedure finds weaknesses, assesses what has to be fixed, and sets up scanning frequencies to look for emerging threats. Prioritizing vulnerabilities based on their impact and business significance ensures efficient allocation of resources. To lower risks and improve security, a mitigation strategy must be put into place after it has been prioritized. Examples of this include deploying patches or isolating areas. By using this method, the system’s susceptibility to cyberattacks is reduced, and time is gained to address the core issues.
Step 2. Prioritize: In order to stop hackers from potentially using vulnerability management to compromise data or interfere with operations, vulnerability management is an essential component of corporate cybersecurity. Following best practices in the vulnerability assessment lifecycle enhances an organization’s ability to identify and promptly resolve vulnerabilities. Making an inventory of all enterprise assets, such as servers, network equipment, software, and hidden IT assets, is the first step in the process. Identifying assets with the biggest risks, considering elements like company operations and reputational risk, is critical. An efficient route to remediation is determined by giving priority to these assets and adding threat intelligence and root cause analysis to the scan data. An organization’s resistance to possible dangers is strengthened by putting this all-encompassing strategy into practice.
Step 3. Act: Organizations must use vulnerability management, a comprehensive cybersecurity strategy, to successfully detect and stop cyberattacks before they happen. A strong vulnerability management software, in contrast to periodic vulnerability scanning, continuously identifies, evaluates, prioritizes, and fixes flaws before attackers can take advantage of them. Organizations need to adopt a structured vulnerability management methodology in order to handle the startling 21,957 vulnerabilities found in commercial software and hardware and stay ahead of the constantly changing threats. This guarantees that resources are allocated to the assets that pose the greatest cybersecurity concerns. Although it is not feasible to deploy every security patch, a robust vulnerability management strategy offers the structure, accuracy, and rationale required for continuous security actions. Starting with the vital process of creating an asset inventory, this article explores the six critical elements of the vulnerability management lifecycle.
Step 4. Reassess: After creating an asset inventory, organizations use threat intelligence platforms and conventional vulnerability scans to identify and rank vulnerabilities in code. Throughout the program’s lifespan, effective communication between teams and with stakeholders is essential for facilitating seamless transitions and discussions about changes. Although it is desirable to fix all vulnerabilities right away, there are practical limitations, such as waiting for vendor fixes, that call for a more realistic approach. During this waiting period, putting risk mitigation mechanisms in place helps lessen the possible effects of vulnerabilities. This well-balanced approach actively manages and minimizes risks while acknowledging the constraints of resources.
Step 5. Improve: Security teams take action by testing and repairing these flaws, bolstering cyber defenses, and clearing backlogs after evaluating and ranking vulnerabilities. Repeating vulnerability scans on a regular basis—ideally with automation for efficiency—guarantees that any recently missed threats will be found. Creating an asset inventory of business-critical systems is the second phase, which helps find unapproved systems and asset management gaps. This inventory also determines the criticality of each asset, aiding in the prioritization of pressing issues. By offering a focused approach to fixing vulnerabilities and strengthening the security posture, this proactive approach to vulnerability management improves the organization’s resilience against possible cyber threats.
WHY IS VULNERABILITY MANAGEMENT IMPORTANT?
Organizations are focusing more on information security as the threat of cybercrime grows and regulatory scrutiny increases. An effective vulnerability management strategy must be integrated into the field of information risk management.
Through this method, firms can continuously identify vulnerabilities in their IT infrastructure and evaluate the risks that come with them. Mitigating and proactively identifying vulnerabilities is crucial in order to reduce the likelihood of potential attacker exploitation. Resolving vulnerabilities effectively entails patching on time, making use of databases such as CVE and others, and forming a strong risk management plan to reduce cybersecurity risks and improve overall resilience.
CERTPRO assists in keeping up strong security procedures and compliance.
CertPro offers a variety of services to help businesses improve their vulnerability management process as a recognized industry leader in vulnerability management solutions. We also provide guidance on how to create strong vulnerability management policies and implement strong vulnerability management solutions into practice. To find any holes or non-compliance issues in an organization’s security architecture and ensure they follow the rules of thorough risk management, we conduct in-depth evaluations and precise audits.
In order to ensure that organizations build strong vulnerability management policies that are in line with industry best practices, CertPro specializes at coaching them through the challenging process of improving their vulnerability management processes. Our objective is to help enterprises effectively detect and mitigate vulnerabilities so that they are better able to manage the constantly changing landscape of cybersecurity threats.
FAQ
What are the key components of Vulnerability Management?
The key components include discovery (identifying all assets), assessment (evaluating vulnerabilities), prioritization (ranking vulnerabilities), remediation (addressing vulnerabilities), and monitoring (continuous vigilance).
What are the benefits of vulnerability management offer?
Vulnerability Management enhances security, ensures regulatory compliance, reduces costs, and enhances an organizations reputation by demonstrating a commitment to data protection.
What role does employee training play in vulnerability Management?
Employee training is crucial to mitigating human errors in cybersecurity. It educates employees about the importance of cybersecurity and fosters a security-conscious culture.
How can CertPro assist with Vulnerability Management?
CertPro, an expert in vulnerability management, provides services to enhance organizations vulnerability management, offering guidance, assessments, audits, and policy improvement
Why is proactive Vulnerability Management crucial in today's cybersecurity landscape?
Proactive vulnerability Management is crucial in the ever-changing cybersecurity landscape. Identifying and addressing vulnerabilities preemptively safeguards systems and data from emerging threats.

About the Author
NICOLENE KRUGER
Nicolene Kruger, Regional Manager in South Africa, is an experienced Legal Counsel with expertise in compliance and auditing. Her strategic, solution-driven approach aligns legal standards with business objectives, ensuring seamless adherence to regulations.
HOW DOES THE NIST CYBERSECURITY FRAMEWORK FUNCTION, AND WHY IS IT IMPORTANT?
Emerging cyber threats make cybersecurity an essential consideration for organizations handling and managing data. In this regard, the NIST cybersecurity framework applies to improving your cybersecurity program. It is a set of guidelines that helps improve your...
UNDERSTANDING ISO 42001: A GUIDE FOR RESPONSIBLE AI MANAGEMENT SYSTEMS
The invention of artificial intelligence (AI) has changed the operational processes of many industries. However, the rapid growth of technology increases ethical, security, and privacy-related concerns. Therefore, the International Organization for Standardization...
EUROPEAN UNION’S ARTIFICIAL INTELLIGENCE ACT: HOW THIS GROUNDBREAKING LAW AFFECTS YOUR BUSINESS
Nowadays, Artificial Intelligence (AI) is transforming our lives exceptionally well. AI is now streamlining healthcare services, providing virtual assistance, and fulfilling queries. Technologies have boons and curses. Similarly, AI creates many concerns about...