Due to a number of queries on VAPT, we would like to cover some of the basic elements of VAPT. ‘What is VAPT?’, ‘what are VAPT tools?’, ‘what is the difference between VA and PT?’, ‘how can we conduct VAPT internally, externally & by a third party?’, ‘what is black box VAPT, grey box VAPT, white box VAPT?’ etc are some of the multiple questions that we constantly receive through our enquiry boxes. For all these questions and many more, you can always refer our website for relevant answers including the methodology used for each of these processes.
What is VAPT? What is the difference between VA & PT?
VA – Vulnerability Assessment (VA) is a process set with the goal of finding the loopholes in your IT infrastructure: it could be in your application, software system, network, etc.
PT- Penetration Testing (PT) is the test conducted to investigate the severity of the loopholes found by VA testing.
Let us give you a simple example to understand it better;
VA testing identifies weak cryptography in the host. Penetration testing tools can be used to identify how it will impact the system. If it is decoded to gain access to the database (similar to a phishing attack), then it could be a potential threat.
VA is a list of loopholes whereas PT identifies the severity of each loophole.
What are VAPT tools?
VAPT tools are tools that automatically identify the vulnerability in the system and also generate a report on penetration testing. It can also be limited to specific tasks (with a popular tool like Nessus). VAPT tools work as an IT admin for small startups to identify the threats in the IT infrastructure of an organization. There are a number of VAPT tools available now in the market. To get the best results, we recommend you seek a professional opinion on VAPT before you opt for any in-house tool.
Some of the pros and cons of VAPT Tools are given below:
Pros
- Easily available
- Open-source applications are available.
- On adding the IP addresses, reports are auto-generated within minutes to a few hours.
- Manual expertise is not required since it is automated & shows the end results in the form of reports.
- Easily helps to understand the IT environment for small scale companies (even a non-IT firm can operate these tools)
Cons
- Data security could be compromised since you will be sharing the IP information to suspicious tools without any agreement.
- Free application results may not be accurate.
- Penetration testing could open the portals which may entertain the hackers. It is important to close all the portals after testing (some tools fail to do so).
- Some of the tools are expensive to own and sensitive for beginners.
It is always advisable to consult a third-party professional with a formal agreement like a non-disclosure agreement that is mutually beneficial for both the parties in terms of service, time, resource and legal requirements.
You can always reach us for any such queries at https://sitemunky.com/certproind/contact-us/
What is internal vulnerability assessment, external vulnerability assessment & Third-party Assessment In VAPT?
Internal vulnerability assessment is the process of testing your IT security internally. Internal vulnerability assessment evaluates the IT security from inside the company (internal software, network, employee competence, work environment & internal policy in terms of IT security, etc.)
External vulnerability assessment evaluates IT security outside the company. This includes identifying the loopholes in your network firewall wherein the malicious outsiders can break in and attack your network and other business-related confidential information.
Both are done by a third party. It is recommended that companies approach a third-party expert for their technical audits. We also suggest doing the VAPT on a regular basis. Internal VAPT assessment can be done for more accurate manual results which include identifying human errors and work etiquette. These professionals are well equipped with the right tools to handle your requirements depending on the scope of your business and work activities. Once these loopholes are closed, professionals always recommend that you re-assess the same for better results in the future.
What is Black box testing, Grey testing & White box testing in VAPT?
- Black box testing: Testing from the external network without the knowledge of the internal networks & the system.
- Grey box testing: Testing can be done either by external or internal networks, with the knowledge of your internal network and system. Grey box testing is a combination of both the black box and the white box.
- White box testing: Testing from the internal network with the knowledge of the internal network & the system.
It is better to discuss these with professionals so that you accurately understand the relevant mode of testing for your organization.
Is VAPT mandatory in ISO 27001 or any IT related standards? What are the benefits of VAPT in ISO or any standard compliance?
VAPT can become the proof of evidence for many technical controls. For example, ISO 27001:2013 information security management system (ISMS) statement of applicability (SOA) defines the controls under which A12.6 speaks particularly about vulnerability management. Similarly, the control A12.6.1 defines the integrity, security, availability and the vulnerability associated with internal and external threats. Testing is mandatory to identify the internal and external risks associated with it and appropriate measures are to be taken. A12.6.2 defines the controls on software and it has to be verified before opting for any useful work.
We can relate VAPT with many controls in ISO 27001. Examples include A13.1 Network security, A14.2.3 Technical review of applications after operating platform changes, A14.2.9 System acceptance testing etc.
A single report of VAPT can be the proof of many technical controls of the organization. It is not limited to ISO 27001 but also for other certifications including SOC, PCI-DSS, HITRUST, GDPR, HIPAA etc.
WHAT IS THE VAPT REPORT? HOW TO GET A VAPT CERTIFICATE OR VAPT COMPLIANCE? HOW FREQUENTLY CAN VAPT BE DONE?
VAPT report details all the results of your vulnerability assessments and penetrating testing. This report is highly beneficial to build the confidence of your clients.
VAPT compliance can be gained through an assessment certificate from a third party. But, holding a certificate would never amount to anything if the company does not really understand the risks in their IT infrastructure. It is better to get a VAPT report from an expert where you are guided properly and subsequently you are able to understand the whole process (including the potential risks in your organization). Cheap certificates will do more harm than good.
VAPT can be done on a daily, weekly, monthly or yearly basis. It mainly depends on the nature of your work activities and the necessity of a VAPT. We suggest you get it done twice a year along with your internal & technical audits.
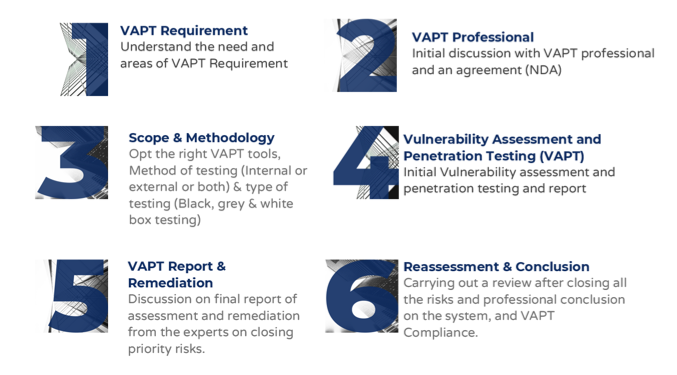
How to get VAPT compliance or VAPT certification?
HOW DOES THE NIST CYBERSECURITY FRAMEWORK FUNCTION, AND WHY IS IT IMPORTANT?
Emerging cyber threats make cybersecurity an essential consideration for organizations handling and managing data. In this regard, the NIST cybersecurity framework applies to improving your cybersecurity program. It is a set of guidelines that helps improve your...
UNDERSTANDING ISO 42001: A GUIDE FOR RESPONSIBLE AI MANAGEMENT SYSTEMS
The invention of artificial intelligence (AI) has changed the operational processes of many industries. However, the rapid growth of technology increases ethical, security, and privacy-related concerns. Therefore, the International Organization for Standardization...
EUROPEAN UNION’S ARTIFICIAL INTELLIGENCE ACT: HOW THIS GROUNDBREAKING LAW AFFECTS YOUR BUSINESS
Nowadays, Artificial Intelligence (AI) is transforming our lives exceptionally well. AI is now streamlining healthcare services, providing virtual assistance, and fulfilling queries. Technologies have boons and curses. Similarly, AI creates many concerns about...