The digital world presents a wealth of opportunities for businesses. It could be global customer connections and streamlined operations. However, this opportunity comes with a critical responsibility. Service providers need to safeguard the data and systems. This is where security compliance comes in. Therefore, it can create a more secure place for your business and its valuable assets in this digital platform. These compliance guidelines can be set internally or required by external regulations, depending on your industry and location. Hence, following these standards showcases the organization’s data security and privacy dedication. It helps in creating business relationships.
This blog will guide you through the world of security compliance in depth. We’ll also guide you through the essential steps for your business. After reading the article, you will understand the necessity of ensuring regulatory standards. More importantly, you might be capable of building a solid security posture for your business.
UNDERSTANDING SECURITY COMPLIANCE
Simply put, security compliance means following rules designed to keep your customer data secure. Thus, governments or industry groups can create these rules. Therefore, by following compliance guidelines, your business prioritizes data security. It protects information from unauthorized access and maintains data confidentiality.
There are two main drivers for security compliance:
- Regulations: Many industries have specific regulations that mandate data security practices. These regulations depend on data regions and the organization’s location. Thus, ignoring these regulations can result in severe consequences for your business.
- Best Practices: Even without strict regulations, following strong security practices in your industry can build trust with customers and partners. Accordingly, strong security is a competitive advantage for your business in this data-driven world.
Furthermore, you can consider security compliance a protector of your data and organization. It provides measures to stay protected from cyberattacks and uncertain situations.
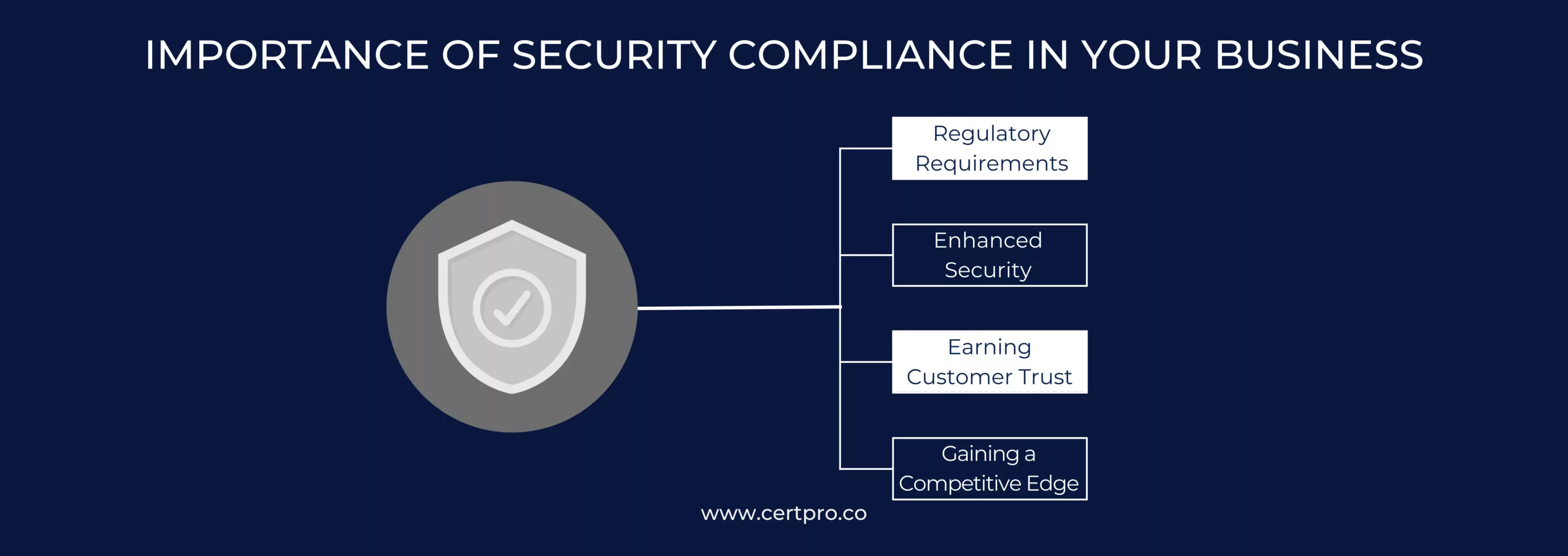
IMPORTANCE OF SECURITY COMPLIANCE IN YOUR BUSINESS
Security compliance isn’t just about following rules and avoiding penalties. It’s about creating a solid foundation for data security within an organization. Here’s why prioritizing compliance is vital for organizations:
- Regulatory Requirements: Many industries have strict data security regulations, which are essential for protecting customers’ sensitive information. These regulations are framed by regulatory bodies, which have the right to impose fines for non-compliance. Not following these rules can increase the risk of data breaches and even legal trouble for your business. Hence, following these regulations will protect you from financial and reputational failures.
- Enhanced Security: Security compliance involves setting up various security measures, such as firewalls, threat detection systems, and data encryption. The whole process works together to safeguard your customers’ information. It acts as a barrier through which cyber criminals cannot manipulate sensitive data. Furthermore, these controls mandate regular security assessments to measure and identify weaknesses in your system. Therefore, giving more importance to security compliance helps your business meet the requirements. Also, it enables you to create a robust security system, eventually reducing the chances of a data breach.
- Earning Customer Trust: It is essential to note that customers are now prioritizing their data safety, so your business needs to maintain data security as its top priority. A data breach can affect the trustworthiness of your organization. Subsequently, it can lead to reputational damage and restrict business growth. Therefore, implementing security compliance regulations shows your commitment to data safety. Similarly, it assures customers about their data safety and handling process. Thus, shortly, it will help bring customers and uphold trust and loyalty.
- Gaining a Competitive Edge: Security compliance isn’t just about penalties and legal trouble but also a strategy that benefits your security system. Many businesses require their partners and vendors to comply with security compliance regulations. Therefore, achieving compliance certifications unlocks many opportunities and partnerships for your organization. Likewise, you can ensure your business’s long-term security and success by prioritizing security compliance regulations.
SECURITY COMPLIANCE LAWS AND STANDARDS FOR YOUR KNOWLEDGE
As we discussed the importance of compliance, it’s time to figure out which security framework best suits your business. However, multiple regulations and frameworks are available for securing data. Therefore, choosing the proper framework for your business becomes difficult. In this respect, you can seek professional help to find a more acceptable framework for your organization. Here, we mention the fundamental security compliance laws and standards for your knowledge:
1. General Data Protection Regulation (GDPR): The European Union implemented the GDPR in 2018. Therefore, GDPR prevents the risk of unauthorized access to data, discourages data manipulation, and maintains privacy. Organizations must handle and manage data from European residents. The penalty for non-compliance is around 4% of your organization’s annual revenue or 20 million euro.
2. California Consumer Privacy Act (CCPA): This regulation applies to organizations with more than $25 million in annual revenue or those processing massive data. Similarly, it is mandatory for organizations related to Californian citizens. Therefore, the regulation supports the right to control personal data. Furthermore, if an organization cannot comply with CCPA, it can face hefty fines. In 2023, an amendment was made to CCPA, prohibiting the unnecessary retention of customer data for a prolonged period.
3. Service Organization Controls (SOC) Reports: These reports indicate that the service provider has attempted third-party audits and executes specific security measures for their organization. Therefore, SOC compliance ensures that the organization prioritizes data security. In addition, it accesses the security measures of the organizations to strengthen the data security aspect.
4. Health Insurance Portability and Accountability Act (HIPAA): This federal law protects patients’ sensitive data disclosure. Therefore, implementing HIPAA suggests that digital health information is safe and secure. As a healthcare provider, you must comply with HIPAA. It ensures administrative, physical, and technical safeguards to protect patient data.
5. Payment Card Industry Data Security Standard (PCI DSS): This standard is used to secure financial data. If your business processes, stores, or transmits cardholder data. Compliance with PCI DSS becomes mandatory if you accept credit cards. It helps your organization prevent data breaches and fraud.
6. International Organization for Standardization (ISO) 27001: This internationally recognized standard provides an information security management system (ISMS) framework. It outlines a systematic approach to managing information security risks. Thus, controls are implemented, and an organization’s security posture is continually improved.
ESSENTIAL STEPS FOR SECURITY COMPLIANCE PRACTICES
Now that you have understood the importance and key practices of security compliance, let’s explore the key steps to achieve and maintain it:
1. Identify Applicable Regulations: At the initial stage, you must find suitable regulatory compliance for your business. Therefore, it depends on the organization’s size, complexity, and functionality. If your organization handles European clients’ data, GDPR is helpful. However, HIPAA is perfect for ensuring data security if your organization is related to healthcare services.
2. Conduct a Security Risk Assessment: Evaluating your organization’s security posture is essential. This will help identify potential threats and risks. Therefore, recognizing threats and vulnerabilities helps implement the correct security compliance regulations for your organization.
3. Develop a Security Policy: Develop a thorough security policy for your business’s data security approach. This policy should define the use of IT resources, data access controls, password management protocols, and incident response procedures.
4. Implement Security Controls: Select a security framework based on your risk assessment. These controls may include firewalls, detection systems, and data encryption. Furthermore, it has access controls and employee security awareness training.
5. Regular Monitoring and Auditing: Compliance is not a one-time achievement. Thus, regular monitoring is required to ensure your security controls function effectively. Furthermore, the process can identify potential gaps that may risk security.
6. Incident Response Planning: The risks of data breaches are uncertain. Therefore, a strong security posture and an appropriate incident response plan will reduce these risks. They help mitigate risks and restore operations.
7. Seeking Professional Help: Professional guidance can make your procedure smooth and easy. Consider seeking help from security professionals to assess your risks. Discuss the additional requirements, develop a compliance strategy, and implement necessary controls.
8. Maintaining Compliance: The final step is to stay updated on regulatory changes. Regular monitoring is crucial for proper functionality, and employees should be educated about new upgrades.
Security compliance safeguards your organization and reduces the impact of cyber threats. In addition, implementing security tools and regulations may need to be more efficient in preventing data breaches. The organization must regularly assess the implemented regulations and policies. This helps recognize the threats and mitigate them through security compliance. Consequently, compliance is an ongoing process for any business. Therefore, it is essential to be committed to the requirements that security regulations demand.
Furthermore, the regulations and the vital steps mentioned in this blog can safeguard your business. Develop a culture of security awareness by minimizing security risks. It will ensure data safety and confidentiality in this ever-evolving digital world.

FAQ
Is security compliance exclusively about avoiding fines?
Not entirely. Compliance helps avoid fines but is more about building a strong security foundation. It minimizes data breaches and protects your reputation, ultimately benefiting your business.
What steps do I take to ensure that my business is compliant?
Conduct a security risk assessment to identify gaps. Regularly monitor your systems and conduct audits to ensure controls work effectively.
What is security compliance management?
Security compliance management is a series of policies and controls that address your organization’s data protection and security. It prevents the consequences of data breaches and upholds the reputation.
How long does it take to become compliant?
There’s no one-size-fits-all answer. It depends on your existing security posture and chosen framework. Compliance is an ongoing process, not a one-time achievement.
How much does achieving security compliance cost?
Costs vary depending on regulations, business size, and existing security measures. It can involve investments in technology, training, and potentially professional guidance.

About the Author
NICOLENE KRUGER
Nicolene Kruger, Regional Manager in South Africa, is an experienced Legal Counsel with expertise in compliance and auditing. Her strategic, solution-driven approach aligns legal standards with business objectives, ensuring seamless adherence to regulations.
HOW DOES THE NIST CYBERSECURITY FRAMEWORK FUNCTION, AND WHY IS IT IMPORTANT?
Emerging cyber threats make cybersecurity an essential consideration for organizations handling and managing data. In this regard, the NIST cybersecurity framework applies to improving your cybersecurity program. It is a set of guidelines that helps improve your...
UNDERSTANDING ISO 42001: A GUIDE FOR RESPONSIBLE AI MANAGEMENT SYSTEMS
The invention of artificial intelligence (AI) has changed the operational processes of many industries. However, the rapid growth of technology increases ethical, security, and privacy-related concerns. Therefore, the International Organization for Standardization...
EUROPEAN UNION’S ARTIFICIAL INTELLIGENCE ACT: HOW THIS GROUNDBREAKING LAW AFFECTS YOUR BUSINESS
Nowadays, Artificial Intelligence (AI) is transforming our lives exceptionally well. AI is now streamlining healthcare services, providing virtual assistance, and fulfilling queries. Technologies have boons and curses. Similarly, AI creates many concerns about...