Information security is critical in the ever changing digital world where data is the foundation for both individuals and companies. Putting strong security measures in place requires a multifaceted approach, and security models are the foundation of this defense. These frameworks function as architectural blueprints that outline how security principles should be implemented inside systems or organizations to maintain the core information assets of confidentiality, integrity, and availability (also known as the CIA triad).
This blog provides readers with a comprehensive understanding of models of security, exploring their diverse varieties, practical applications, and inherent benefits in fortifying digital infrastructures against potential attacks, offering a deep dive into the intricate realm of types of security models.
WHAT IS SECURITY MODELS?
Information security models serve as intricate systems designed to delineate and regulate the allocation of data access to individuals, while also governing the operational functionality of the underlying operating system, thereby empowering management to effectively organize and enforce access control measures. These models extend beyond mere conceptual frameworks, offering a nuanced understanding of how security protocols are translated into practice within specific contexts, providing a sophisticated mathematical framework that aligns theoretical security objectives with practical implementation strategies. In essence, security models serve as foundational pillars within the realm of cybersecurity, intricately shaping the landscape of data protection and fortification against potential threats by offering a structured approach to security enforcement, bolstered by mathematical mappings of theoretical goals to strengthen the chosen implementation methodology.
It provides a structured approach to securing information assets by outlining:
- Subjects: These are the entities that make up the active agents that access or modify information in the system, including users, processes, and applications. They interact and impact data and systems, constituting the dynamic elements of security architecture.
- Objects: Objects are the passive components of the security model, representing the information assets that are protected, such as data, files, and systems. As such, they must be protected from unauthorized access or alteration.
- Operations: Subject-performed actions on objects that include basic functions like read, write, and execute. These operations are essential to preserving data integrity and secrecy because they specify what may be done on objects by subjects.
- Control mechanisms for access: These regulate the permission levels and rights assigned to system entities, as well as the rules that dictate how subjects and objects interact. Assuring that only authorized organizations are permitted access, they serve as the foundation of security enforcement.
- Security policies: High-level guidelines that serve as the overall directives that create the security posture and specify acceptable security behavior inside the system. By laying out the bounds of appropriate behavior, these rules successfully reduce risks by coordinating corporate goals with security measures.
Through the formalization and integration of these components, models of security provide a thorough framework for comprehending the information flow inside the system and the accompanying controls implemented to successfully protect its integrity and confidentiality.
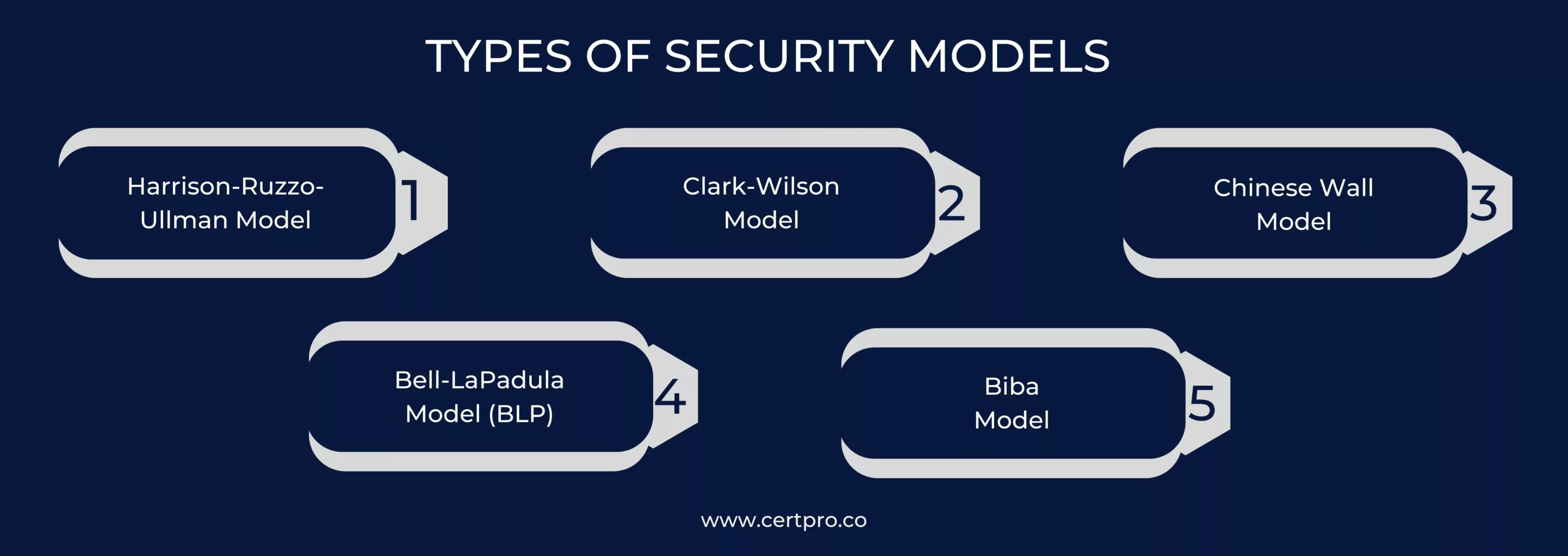
TYPES OF SECURITY MODELS
The field of security has a wide range of intricate aspects that necessitate a variety of security model types to meet different needs. We detail a number of noteworthy categories within the security model spectrum below.
1. Harrison-Ruzzo-Ullman Model: The Harrison-Ruzzo-Ullman Model, often considered an extension of the BLP model, complements the BLP’s lack of mechanisms for altering access rights or managing subjects and objects by introducing an authorization system to allocate access rights and ensure compliance with specified policies, thus addressing security concerns regarding information flow. Operating on discretionary access control principles, the HRU model employs an access matrix to determine permissible actions that subjects, like users, can execute on objects, offering flexibility in managing access controls within systems and demonstrating another approach within types of security models.
2. Clark-Wilson Model: The Clark-Wilson Model, falling under types of security models, delineates between constrained data items (CDIs) and unconstrained data items (UDIs), alongside two transaction types: Integrity Verification Procedures (IVPs) ensuring the validity of Transaction Procedures (TPs) resulting from CDIs, with only authorized TPs permitted to manipulate CDIs, thus establishing a framework for safeguarding information integrity against hostile data-altering attempts, formalizing integrity policies to maintain data validity across system states, and specifying certification and enforcement procedures as well as the roles and capabilities of system principals.
3. Chinese Wall Model: The Chinese Wall Model, also known as the Brewer and Nash model, within the realm of types of security models, emphasizes conflict of interest avoidance by restricting access to confidential information belonging to separate stakeholders, with access control policies dynamically adjusting based on user behavior to prevent access to conflicting data, promoting data segregation and dynamic access controls in response to user interactions with critical information, although it is not as commonly adopted as other models of security.
4. Bell-LaPadula Model (BLP): Bell-LaPadula is a traditional Mandatory Access Control (MAC) security model that emphasizes confidentiality. It is defined by three main properties: the *-property (star-property), which focuses on preventing “write-down” access; the DS-property, which addresses discretionary security; and the SS-property, which addresses simple security or the prohibition of “read-down” access. A system that complies with BLP must meet all of these properties. The only true implementation of the model can be found in Honeywell Multics, though it has not been widely adopted. This highlights the model’s strict control over information flow, where subjects are unable to downgrade information or change security levels once instantiated, creating a framework for secure information handling within classified environments.
5. Biba Model: The Biba Model, a complementary Mandatory Access Control (MAC) framework emphasizing data integrity, delineates integrity levels and access principles analogous to BLP but in reverse, featuring the Simple Integrity Property where subjects are barred from writing to objects at lower levels, the *-Property prohibiting subjects from reading objects at higher levels, and the Discretionary Integrity Property preventing objects from being elevated in integrity level, thereby providing a comprehensive structure for safeguarding data integrity within secure environments.
Types of Security Models encompass a broad range of approaches beyond those mentioned, tailored to address diverse security needs such as network security, multi-level security, and attribute-based access control, among others, reflecting the varied requirements of securing information and resources across different contexts.
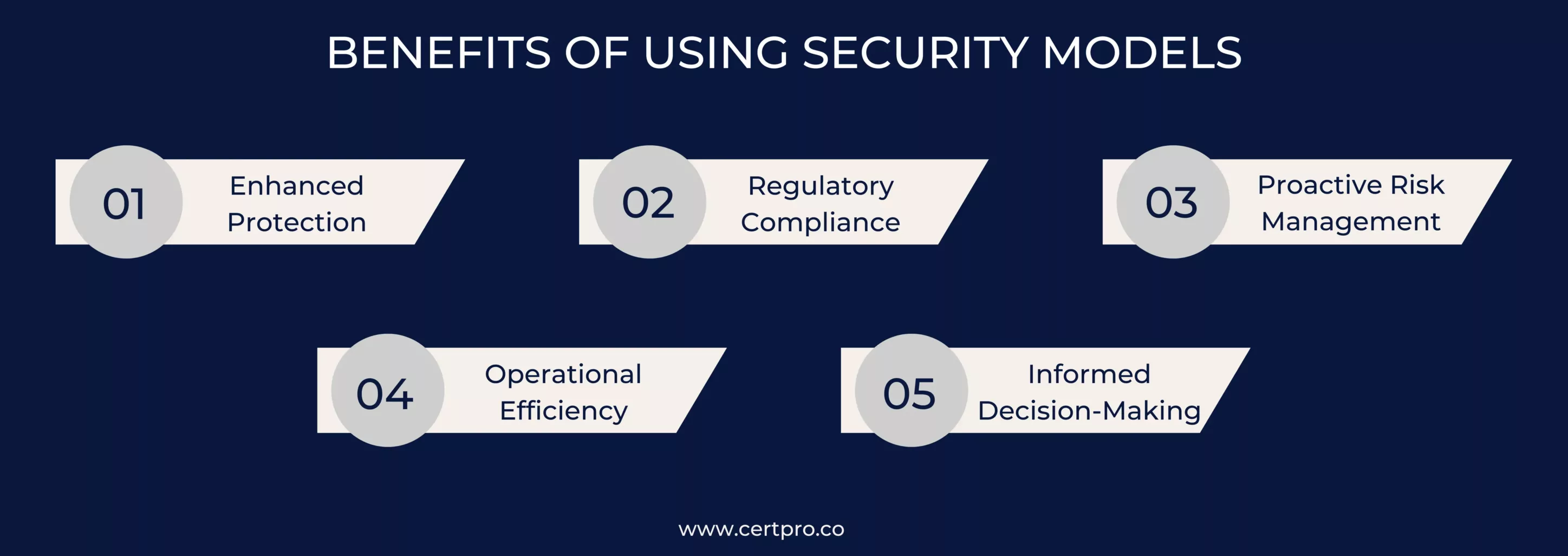
BENEFITS OF USING SECURITY MODELS
Utilizing various types of model security offers numerous advantages for organizations seeking to bolster their defenses against cyber threats:
1. Enhanced Protection: By addressing several layers of possible vulnerabilities and attack vectors, the implementation of a mix of security models strengthens the overall security posture of an organization. The probability of successful breaches or unauthorized access is decreased by this multi-layered strategy.
2. Regulatory Compliance: In order to facilitate compliance with legal and industrial rules, various security frameworks are frequently in line with certain regulatory requirements and compliance standards. Organizations may show their dedication to protecting sensitive data and fulfilling legal requirements by using these models.
3. Proactive Risk Management: Models of security enable organizations to identify and mitigate potential security risks in a proactive manner. By leveraging established frameworks and best practices, businesses can anticipate and address emerging threats before they escalate into significant security incidents.
4. Operational Efficiency: Implementing security models streamlines security processes and procedures leading to improved operational efficiency. These models provide standardized guidelines and methodologies, reducing the time and resources required for security planning, implementation, and maintenance.
5. Informed Decision-Making: Familiarity with different types of security models empowers organizations to make well-informed decisions regarding their security infrastructure and strategies. By understanding the strengths and limitations of each model, businesses can tailor their security approach to suit their unique requirements and risk profiles.
All things considered, an organization’s capacity to protect itself against constantly changing cyberattacks, remain compliant with laws, and maximize operational effectiveness is strengthened by the deliberate use of a variety of security models.
8 FACTORS TO CONSIDER WHEN SELECTING THE RIGHT SECURITY MODEL?
Security models have many advantages, but the proper model must be selected for your particular requirements in order for them to be successful. Consider the following important factors:
1. Evaluate the Requirements: Starting with a thorough and comprehensive assessment of the security requirements that are inherent to your organization is essential to starting the process of choosing the right security model. This assessment should cover a detailed examination of factors like regulatory compliance obligations, industry standards adherence, data sensitivity levels, and an analysis of the organization’s risk tolerance thresholds.
2. Determine the Threat Condition: In order to ascertain the threat landscape that your organization is facing, it is imperative that you carry out an extensive analysis that covers a multitude of aspects, such as the appraisal of newly emerging cyber threats, the scrutiny of past attack patterns, and the appraisal of potential vulnerabilities that may jeopardize the security posture of the organization.
3. Recognize Security Models: To become well-versed in models of security, one should thoroughly investigate the many varieties of these models, exploring their fundamental ideas, advantages, and disadvantages. Some examples of popular models are the Bell-LaPadula model, the Biba model, the Clark-Wilson model, and the Role-Based Access Control (RBAC) model.
4. Determine Requirements with Models: When assessing the suitability of each security model, it is essential to conduct a thorough evaluation of how well each model corresponds to the unique requirements and objectives of your organization, taking into account various factors such as scalability, flexibility, ease of implementation, and compatibility with existing systems and processes, in order to make an informed decision that optimally aligns with your organization’s security needs.
5. Examine Industry Best Practices: Include a review of industry best practices and standards relevant to your company’s industry in your decision-making process by researching frameworks like the NIST Cybersecurity Framework, ISO/IEC 27001, or PCI DSS in detail. These established guidelines provide important information and suggestions for choosing appropriate security frameworks and putting in place strong security measures that are customized to your company’s requirements.
6. Seek Professional Guidance: Speak with consultants, security specialists, or colleagues in the field who have chosen and used security approaches. You may steer clear of typical traps and make better judgments with their advice and insights.
7. Considerations for Budget and Resources: It is necessary to choose a model that not only fits your security requirements but also fits within your budgetary constraints and resource limitations in order to ensure successful implementation and long-term maintenance. A security model’s successful deployment frequently requires the allocation of financial resources and the utilization of specialized expertise, so these factors must be taken into consideration when considering its implementation.
8. Run Pilot Experiments: Before going into full-scale deployment, it is recommended that organizations consider pilot testing or proof-of-concept trials for specific security models. This allows them to evaluate the models’ effectiveness in real-world scenarios, detect any problems or obstacles, and make the necessary modifications to maximize performance and reduce risks before moving forward with more extensive implementation efforts.
APPLICATIONS OF SECURITY MODELS
Model security have wide-ranging applications across different domains, serving critical functions such as:
Network Security: The deployment and administration of diverse defensive mechanisms in the field of network security is significantly influenced by models of security. Incoming and outgoing network traffic filtering rules are established by firewalls using security models, and intrusion detection systems use these models to identify and address any threats. Furthermore, access control lists, or ACLs, govern network resource access by enforcing security regulations derived from pre-established models.
Operating Systems: security frameworks are essential to the operation of operating systems in order to implement access control methods. Operating systems can manage how system resources are allocated and user rights are limited by using access control models. This guarantees the security of private information and system features while reducing the possibility of unwanted access.
Cloud Computing: The adoption of security frameworks is essential for ensuring the security and integrity of data hosted on cloud platforms. Cloud providers leverage these models to establish robust security protocols that govern data privacy, integrity, and availability. By adhering to established security models, cloud services can offer assurance to customers regarding the protection of their data against potential threats and vulnerabilities.
Application Security: The creation and implementation of secure applications depend heavily on security concepts. These models are used by developers in the design and implementation of strong security measures that counteract known vulnerabilities and thwart malevolent attempts. Organizations may improve the overall security posture of their applications and prevent security breaches by incorporating models of security into the software development lifecycle.
Data Security: Organizations use model security in the field of data security to protect sensitive data from unwanted access, disclosure, or change. These models offer a framework for putting encryption methods, access restrictions, and data security measures in place to guarantee the availability, confidentiality, and integrity of vital data assets. Organizations may create a strong defense against both internal and external threats to their data infrastructure by implementing comprehensive security frameworks.
Although security models might appear complicated at first, it’s important to comprehend their types, purposes, and applications in order to navigate the always changing field of cybersecurity. Through meticulous model selection and implementation, businesses may notably improve their security posture, safeguard confidential information, and foster stakeholder confidence. Keeping up with security frameworks and best practices will continue to be crucial to protecting our digital assets in an ever-more-connected environment as technology advances.
FAQ
Can security models be customized to suit specific business needs?
Yes, model security can be tailored to meet the unique requirements of different industries, organizational structures, and compliance mandates. Organizations can adapt model security to address specific threats and vulnerabilities relevant to their operations.
How do models of security contribute to regulatory compliance?
Models for ensuring security help businesses align their security practices with regulatory requirements by providing frameworks for implementing controls, enforcing policies, and demonstrating compliance with laws and standards such as GDPR, HIPAA, PCI DSS, and ISO/IEC 27001.
How can businesses ensure the effective implementation of Models for ensuring security?
Businesses can ensure effective implementation of security frameworks by conducting thorough risk assessments, providing ongoing training and awareness programs, regularly updating security policies and procedures, and leveraging cybersecurity professionals for guidance and support.
Are models of security only applicable to large enterprises?
No, Models for ensuring security are relevant to organizations of all sizes, from small businesses to large enterprises. Regardless of scale, every organization can benefit from implementing models of security to protect their assets and mitigate cyber threats.
What are the potential risks of not adopting Models for ensuring security?
Without proper models of security in place, businesses are at risk of data breaches, financial losses, reputational damage, legal penalties, and disruptions to operations. By neglecting cybersecurity measures, organizations leave themselves vulnerable to various cyber threats and attacks.

About the Author
NICOLENE KRUGER
Nicolene Kruger, Regional Manager in South Africa, is an experienced Legal Counsel with expertise in compliance and auditing. Her strategic, solution-driven approach aligns legal standards with business objectives, ensuring seamless adherence to regulations.
HOW DOES THE NIST CYBERSECURITY FRAMEWORK FUNCTION, AND WHY IS IT IMPORTANT?
Emerging cyber threats make cybersecurity an essential consideration for organizations handling and managing data. In this regard, the NIST cybersecurity framework applies to improving your cybersecurity program. It is a set of guidelines that helps improve your...
UNDERSTANDING ISO 42001: A GUIDE FOR RESPONSIBLE AI MANAGEMENT SYSTEMS
The invention of artificial intelligence (AI) has changed the operational processes of many industries. However, the rapid growth of technology increases ethical, security, and privacy-related concerns. Therefore, the International Organization for Standardization...
EUROPEAN UNION’S ARTIFICIAL INTELLIGENCE ACT: HOW THIS GROUNDBREAKING LAW AFFECTS YOUR BUSINESS
Nowadays, Artificial Intelligence (AI) is transforming our lives exceptionally well. AI is now streamlining healthcare services, providing virtual assistance, and fulfilling queries. Technologies have boons and curses. Similarly, AI creates many concerns about...